9.5 Chained
The chained authorization use case is a variation on the explicit authorization use case, where the UserIdentityToken provided to the "Authorization Server" is an AccessToken issued by an "Identity Provider". This is useful in systems where the IT infrastructure manages authentication of users, however, the "Authorization Server" is needed to map the IT users onto system specific Roles.
This use case is illustrated in Figure 32.
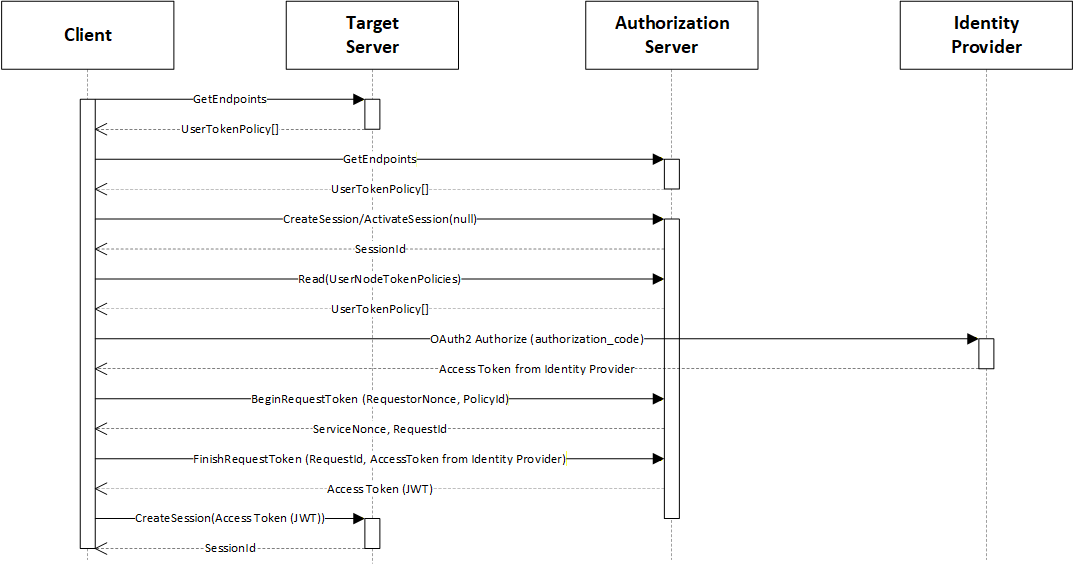
The "Target Server" is the Server that the Client wishes to access. The interactions are the same as with the Explicit authorization use case described in 9.3 except a call to the "Identity Service" is inserted before the Client calls the StartRequestToken Method.
