Introduction
The following table includes new features and the issues resolved with this revision.
| Mantis ID | Scope | Summary | Resolution |
| Feature | Add WoT Actions mapping | Added mapping of WoT Actions to OPC UA server |
1 Scope
This document specifies the OPC UA methods-based configuration API built into industrial connectivity software to map non-OPC UA assets to OPC UA using a Web of Things Thing Description schema to describe the assets. The non-OPC UA assets may have an e.g., Modbus interface, which is specified in the Web of Things Thing Description as a Protocol Binding.
2 Normative references
The following referenced documents are indispensable for the application of this document. For dated references, only the edition cited applies. For undated references, the latest edition of the referenced document (including any amendments and errata) applies.
OPC 10000-1, OPC Unified Architecture - Part 1: Overview and Concepts
http://www.opcfoundation.org/documents/10000-1/
OPC 10000-2, OPC Unified Architecture - Part 2: Security Model
http://www.opcfoundation.org/documents/10000-2/
OPC 10000-3, OPC Unified Architecture - Part 3: Address Space Model
http://www.opcfoundation.org/documents/10000-3/
OPC 10000-4, OPC Unified Architecture - Part 4: Services
http://www.opcfoundation.org/documents/10000-4/
OPC 10000-5, OPC Unified Architecture - Part 5: Information Model
http://www.opcfoundation.org/documents/10000-5/
OPC 10000-6, OPC Unified Architecture - Part 6: Mappings
http://www.opcfoundation.org/documents/10000-6/
OPC 10000-7, OPC Unified Architecture - Part 7: Profiles
http://www.opcfoundation.org/documents/10000-7/
Web of Things Thing Description Specification
https://www.w3.org/TR/wot-thing-description11/
WoT Binding, Web of Things Protocol Binding
https://w3c.github.io/wot-binding-templates/
3 Terms, abbreviated terms and conventions
3.1 Overview
It is assumed that basic concepts of OPC UA information modelling and W3C Web of Things are understood in this document. This document will use these concepts to describe the Web of Things for OPC UA Information Model. For the purposes of this document, the terms and definitions given in OPC 10000-1, OPC 10000-3, OPC 10000-4, OPC 10000-5, as well as the following apply.
Note that OPC UA terms and terms defined in this document are italicized in the document.
3.2 WoT Connectivity for OPC UA terms
3.2.1 Protocol Binding
3.2.2 Part of Web of Things Thing Description describing the communication interface as well as the data “tags” available in an asset.
3.3 Abbreviated terms
| CoAP | Constrained Application Protocol |
| DDL | Device Description Language |
| DTDL | Digital Twin Description Language |
| ERP | Enterprise Resource Planning |
| GDL | Generic Description Language |
| HMI | Human Machine Interface |
| HTTP | Hyper Text Transfer Protocol |
| JSON | JavaScript Object Notation |
| MES | Manufacturing Execution System |
| MQTT | Message Queuing Telemetry Transport |
| PMS | Production Management System |
| URI | Uniform Resource Identifier |
| TD | Web of Things Thing Description |
| W3C | World Wide Web Consortium |
| WoT | Web of Things |
| XML | Extensible Markup Language |
3.4 Conventions used in this document
3.4.1 NodeIds and BrowseNames
3.4.1.1 NodeIds
The NodeIds of all Nodes described in this standard are only symbolic names. Annex A defines the actual NodeIds.
The symbolic name of each Node defined in this document is its BrowseName, or, when it is part of another Node, the BrowseName of the other Node, a “.”, and the BrowseName of itself. In this case “part of” means that the whole has a HasProperty or HasComponent Reference to its part. Since all Nodes not being part of another Node have a unique name in this document, the symbolic name is unique.
The NamespaceUri for all NodeIds defined in this document is defined in Annex A. The NamespaceIndex for this NamespaceUri is vendor-specific and depends on the position of the NamespaceUri in the server namespace table.
Note that this document not only defines concrete Nodes, but also requires that some Nodes shall be generated, for example one for each Session running on the Server. The NodeIds of those Nodes are Server-specific, including the namespace. But the NamespaceIndex of those Nodes cannot be the NamespaceIndex used for the Nodes defined in this document, because they are not defined by this document but generated by the Server.
3.4.1.2 BrowseNames
The text part of the BrowseNames for all Nodes defined in this document is specified in the tables defining the Nodes. The NamespaceUri for all BrowseNames defined in this document is defined in 8.2.
For InstanceDeclarations of NodeClass Object and Variable that are placeholders (OptionalPlaceholder and MandatoryPlaceholder ModellingRule), the BrowseName and the DisplayName are enclosed in angle brackets (<>) as recommended in OPC 10000-3.
If a BrowseName is not defined by this document, a namespace index prefix is added to the BrowseName (e.g., prefix '0' leading to ‘0:EngineeringUnits’ or prefix '2' leading to ‘2:DeviceRevision’). This is typically necessary if a Property of another specification is overwritten or used in the OPC UA types defined in this document.
3.4.2 Common Attributes
3.4.2.1 General
The Attributes of Nodes, their DataTypes and descriptions are defined in OPC 10000-3. Attributes not marked as optional are mandatory and shall be provided by a Server. The following tables define if the Attribute value is defined by this document or if it is server-specific.
For all Nodes specified in this document, the Attributes named in Table 1 shall be set as specified in the table.
| Attribute | Value |
| DisplayName | The DisplayName is a LocalizedText. Each Server shall provide the DisplayName identical to the BrowseName of the Node for the LocaleId “en” unless specified differently in the specification. Whether the Server provides translated names for other LocaleIds is server-specific. |
| Description | Optionally a server-specific description is provided. |
| NodeClass | Shall reflect the NodeClass of the Node. |
| NodeId | The NodeId is described by BrowseNames as defined in 3.4.1.1. |
| WriteMask | Optionally the WriteMask Attribute can be provided. If the WriteMask Attribute is provided, it shall set all non-server-specific Attributes to not writable. For example, the Description Attribute may be set to writable since a Server may provide a server-specific description for the Node. The NodeId shall not be writable, because it is defined for each Node in this document. |
| UserWriteMask | Optionally the UserWriteMask Attribute can be provided. The same rules as for the WriteMask Attribute apply. |
| RolePermissions | Optionally server-specific role permissions can be provided. |
| UserRolePermissions | Optionally the role permissions of the current Session can be provided. The value is server-specific and depends on the RolePermissions Attribute (if provided) and the current Session. |
| AccessRestrictions | Optionally server-specific access restrictions can be provided. |
3.4.2.2 Objects
For all Objects specified in this document, the Attributes named in Table 2 shall be set as specified in the Table 2. The definitions for the Attributes can be found in OPC 10000-3.
| Attribute | Value |
| EventNotifier | Whether the Node can be used to subscribe to Events or not is server-specific. |
3.4.2.3 Methods
For all Methods specified in this document, the Attributes named in Table 3 shall be set as specified in the table. The definitions for the Attributes can be found in OPC 10000-3.
| Attributes | Value |
| Executable | All Methods defined in this document shall be executable (Executable Attribute set to “True”), unless it is defined differently in the Method definition. |
| UserExecutable | The value of the UserExecutable Attribute is server-specific. It is assumed that all Methods can be executed by at least one user. |
4 General information about Web of Things and OPC UA
4.1 Introduction to Web of Things
Typically, in classical IoT projects, developers have to face a challenging situation. They have to understand a heterogeneous technology landscape consisting of diverse IoT systems and services from different vendors and manufacturers. This diversity includes variations in communication protocols, data models for payload data exchange, and security requirements. IoT applications are usually developed using high effort applied to a narrow and specific use case. During their lifetime, such applications are difficult to extend, maintain or reuse.
An IoT device's metadata, including all information needed to enable this common abstraction, is documented in what is called WoT Thing Description (TD). The TD is a central building block in the W3C Web of Things and can be considered as the entry point of an IoT instance (much like the index.html of a Web site). It provides information on which data and functions are provided, which protocol is used, how data is encoded and structured, and security mechanism is used to control access, and further machine-readable and human-readable metadata. A TD is expressed in JSON-LD and can be provided by an IoT device itself or hosted externally in a repository such as a TD Directory.
In general, WoT is a protocol agnostic approach and provides a common mechanism to define how specific protocols such as MQTT, HTTP, CoAP or Modbus can be mapped to the WoT’s interaction properties-action-event abstraction.
This mapping and protocol specific metadata are provided by the WoT Binding Templates. A binding template for a specific protocol provides a guideline how a client can activate each WoT interaction abstraction through a corresponding network-facing interface for that protocol.
Please read here to get more background on WoT Binding Templates.
There are of course other device description languages available in the industry, for example Device Description Language (DDL), Generic Description Language (GDL), Digital Twin Description Language (DTDL). Most of them use either an XML or JSON-based schema, so a converter tool to WoT (based on JSON-LD) can be easily built.
4.2 Introduction to OPC Unified Architecture
4.2.1 What is OPC UA?
OPC UA is an open and royalty free set of standards designed as a universal communication protocol. While there are numerous communication solutions available, OPC UA has key advantages:
A state of art security model (see OPC 10000-2).
A fault tolerant communication protocol.
An information modelling framework that allows application developers to represent their data in a way that makes sense to them.
OPC UA has a broad scope which delivers for economies of scale for application developers. This means that a larger number of high-quality applications at a reasonable cost are available. When combined with semantic models such as Web of Things for OPC UA, OPC UA makes it easier for end users to access data via generic commercial applications.
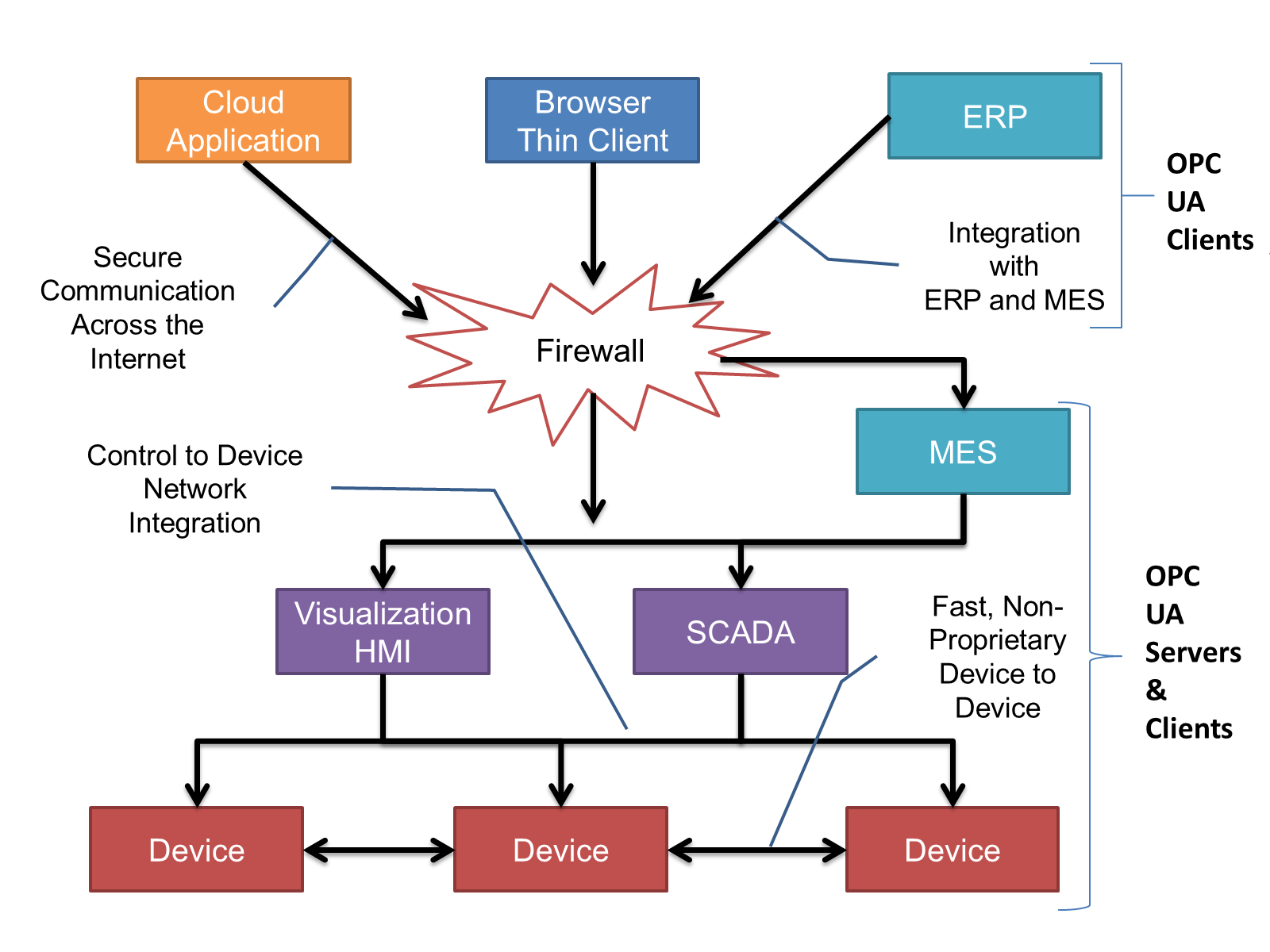
The OPC UA model is scalable from small devices to ERP systems. OPC UA Servers process information locally and then provide that data in a consistent format to any application requesting data, for example ERP, MES, PMS, Maintenance Systems, HMI, Smartphone or a standard Browser. For a more complete overview see OPC 10000-1.
4.2.2 Basics of OPC UA
As an open standard, OPC UA is based on standard internet technologies, like TCP/IP, HTTP, Web Sockets.
As an extensible standard, OPC UA provides a set of Services (see OPC 10000-4) and a basic information model framework. This framework provides an easy manner for creating and exposing vendor defined information in a standard way. More importantly all OPC UA Clients are expected to be able to discover and use vendor-defined information. This means OPC UA users can benefit from the economies of scale that come with generic visualisation and historian applications. This specification is an example of an OPC UA Information Model designed to meet the needs of developers and users.
OPC UA Clients can be any consumer of data from another device on the network to browser based thin clients and ERP systems. The full scope of OPC UA applications is shown in Figure 1.
OPC UA provides a robust and reliable communication infrastructure having mechanisms for handling lost messages, failover, heartbeat, etc. With its binary encoded data, it offers a high-performing data exchange solution. Security is built into OPC UA as security requirements become more and more important especially since environments are connected to the office network or the internet and attackers are starting to focus on automation systems.
4.2.3 Information modelling in OPC UA
4.2.3.1 Concepts
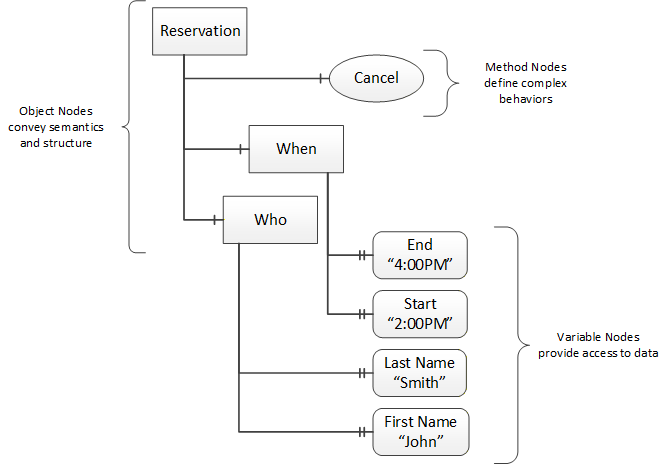
OPC UA provides a framework that can be used to represent complex information as Objects in an AddressSpace which can be accessed with standard services. These Objects consist of Nodes connected by References. Different classes of Nodes convey different semantics. For example, a Variable Node represents a value that can be read or written. The Variable Node has an associated DataType that can define the actual value, such as a string, float, structure etc. It can also describe the Variable value as a variant. A Method Node represents a function that can be called. Every Node has a number of Attributes including a unique identifier called a NodeId and non-localized name called as BrowseName. An Object representing a ‘Reservation’ is shown in Figure 2.
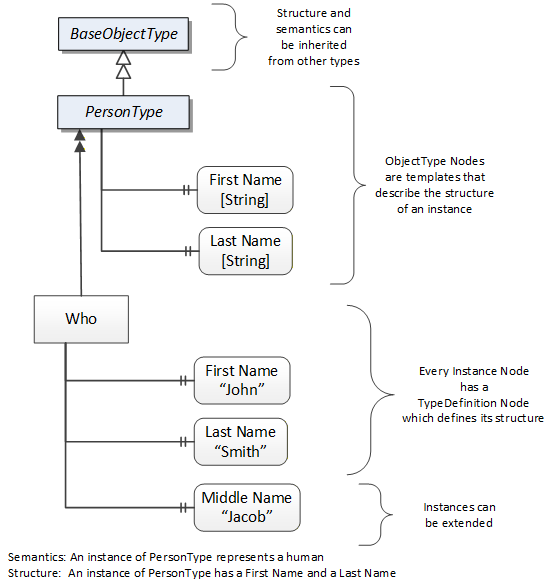
Object and Variable Nodes represent instances and they always reference a TypeDefinition (ObjectType or VariableType) Node which describes their semantics and structure. Figure 3 illustrates the relationship between an instance and its TypeDefinition.
The type Nodes are templates that define all of the children that can be present in an instance of the type. In the example in Figure 3 the PersonType ObjectType defines two children: First Name and Last Name. All instances of PersonType are expected to have the same children with the same BrowseNames. Within a type the BrowseNames uniquely identify the children. This means Client applications can be designed to search for children based on the BrowseNames from the type instead of NodeIds. This eliminates the need for manual reconfiguration of systems if a Client uses types that multiple Servers implement.
OPC UA also supports the concept of sub-typing. This allows a modeller to take an existing type and extend it. There are rules regarding sub-typing defined in OPC 10000-3, but in general they allow the extension of a given type or the restriction of a DataType. For example, the modeller may decide that the existing ObjectType in some cases needs an additional Variable. The modeller can create a subtype of the ObjectType and add the Variable. A Client that is expecting the parent type can treat the new type as if it was of the parent type. Regarding DataTypes, subtypes can only restrict. If a Variable is defined to have a numeric value, a subtype could restrict it to a float.
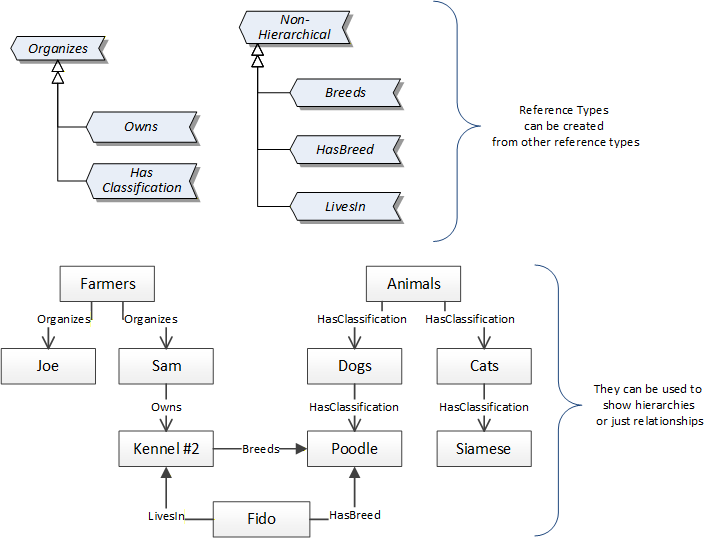
References allow Nodes to be connected in ways that describe their relationships. All References have a ReferenceType that specifies the semantics of the relationship. References can be hierarchical or non-hierarchical. Hierarchical references are used to create the structure of Objects and Variables. Non-hierarchical are used to create arbitrary associations. Applications can define their own ReferenceType by creating subtypes of an existing ReferenceType. Subtypes inherit the semantics of the parent but may add additional restrictions. Figure 4 depicts several References, connecting different Objects.
The figures above use a notation that was developed for the OPC UA specification. The notation is summarized in Figure 5. UML representations can also be used; however, the OPC UA notation is less ambiguous because there is a direct mapping from the elements in the figures to Nodes in the AddressSpace of an OPC UA Server.
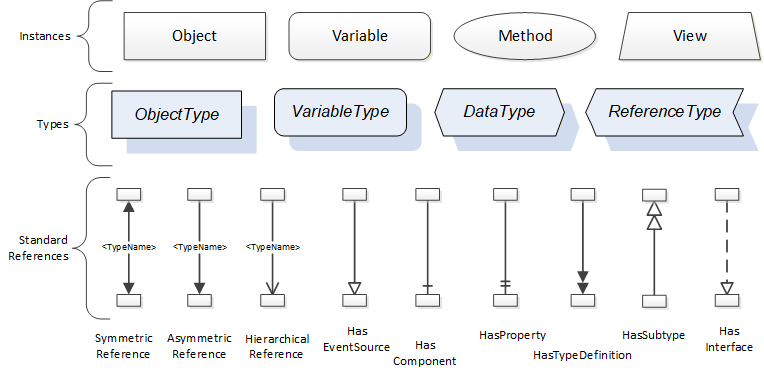
A complete description of the different types of Nodes and References can be found in OPC 10000-3 and the base structure is described in OPC 10000-5.
The OPC UA specification defines a very wide range of functionality in its basic information model. It is not required that all Clients or Servers support all functionality in the OPC UA specifications. OPC UA includes the concept of Profiles, which segment the functionality into testable certifiable units. This allows the definition of functional subsets (that are expected to be implemented) within a companion specification. The Profiles do not restrict functionality but generate requirements for a minimum set of functionalities.
4.2.3.2 Namespaces
OPC UA allows information from many different sources to be combined into a single coherent AddressSpace. Namespaces are used to make this possible by eliminating naming and id conflicts between information from different sources. Each namespace in OPC UA has a globally unique string called a NamespaceUri which identifies a naming authority and a locally unique integer called a NamespaceIndex, which is an index into the Server's table of NamespaceUris. The NamespaceIndex is unique only within the context of a Session between an OPC UA Client and an OPC UA Server- the NamespaceIndex can change between Sessions and still identify the same item even though the NamespaceUri's location in the table has changed. The Services defined for OPC UA use the NamespaceIndex to specify the Namespace for qualified values.
There are two types of structured values in OPC UA that are qualified with NamespaceIndexes: NodeIds and QualifiedNames. NodeIds are locally unique (and sometimes globally unique) identifiers for Nodes. The same globally unique NodeId can be used as the identifier in a node in many Servers – the node's instance data may vary but its semantic meaning is the same regardless of the Server it appears in. This means Clients can have built-in knowledge of of what the data means in these Nodes. OPC UA Information Models generally define globally unique NodeIds for the TypeDefinitions defined by the Information Model.
QualifiedNames are non-localized names qualified with a Namespace. They are used for the BrowseNames of Nodes and allow the same names to be used by different information models without conflict. TypeDefinitions are not allowed to have children with duplicate BrowseNames; however, instances do not have that restriction.
4.2.3.3 Companion Specifications
An OPC UA companion specification for an industry specific vertical market describes an Information Model by defining ObjectTypes, VariableTypes, DataTypes and ReferenceTypes that represent the concepts used in the vertical market, and potentially also well-defined Objects as entry points into the AddressSpace.
5 Use cases
5.1 Communicating with a non-OPC UA asset
OT operators want to communicate with non-OPC UA assets for on-prem or cloud analytics. To do so, a unified data model like OPC UA is desirable as well as a clear description of the asset’s communication protocol and endpoint. Web of Things (WoT) Thing Descriptions (TD) provide such a description and many industrial asset vendors already provide a WoT TD for their products. Secondly, WoT already defines a protocol binding specification for protocols like Modbus or HTTP.
Non-OPC UA assets must be mapped to OPC UA in a (preferably) automated fashion using industrial connectivity software. To achieve this automation, a machine-readable schema fully describing the asset is necessary. For interoperability, a standardized configuration interface, based on OPC UA, is desirable. This can be achieved by specifying a number of OPC UA Methods which are provided in this specification. The industrial connectivity application used to communicate with the asset can then implement these OPC UA Methods to map the asset to OPC UA.
6 WoT Connectivity Information Model overview
6.1 General
The WoT specification defines both a TD and a Protocol Binding.
The WoT TD is defined here:
https://www.w3.org/TR/wot-thing-description/#introduction-td
The WoT Protocol Binding is defined here:
https://www.w3.org/TR/wot-binding-templates/#binding-overview
The goal of this Companion Specification is to create a thin interface for configuring industrial connectivity software in a standardized way. By keeping the interface to a minimum, the chances of adoption by the industry are increased.
{
"@context": [
"https://www.w3.org/2022/wot/td/v1.1"
],
"id": "urn:pac4200",
"securityDefinitions": {
"nosec_sc": {
"scheme": "nosec"
}
},
"security": [
"nosec_sc"
],
"@type": [
"Thing"
],
"name": "modbus-pac4200-sn324",
"base": "modbus+tcp://192.168.178.94:502/1",
"title": "Siemens SENTRON PAC4200",
"properties": {
"Voltage": {
"type": "number",
"readOnly": true,
"observable": true,
"forms": [
{
"href": "7?quantity=2",
"op": [
"readproperty",
"observeproperty"
],
"modv:type": "xsd:float",
"modv:entity": "holdingRegister",
"modv:pollingTime": 2000
}
]
}
}
}6.2 WoT Connectivity entry point
The entry point of this specification in a Server’s object hierarchy is called “WoTAssetConnectionManagement” it is an instance of WoTAssetConnectionManagementType which is defined in 6.3.1
The AddressSpace for the entry point is shown in Figure 6.
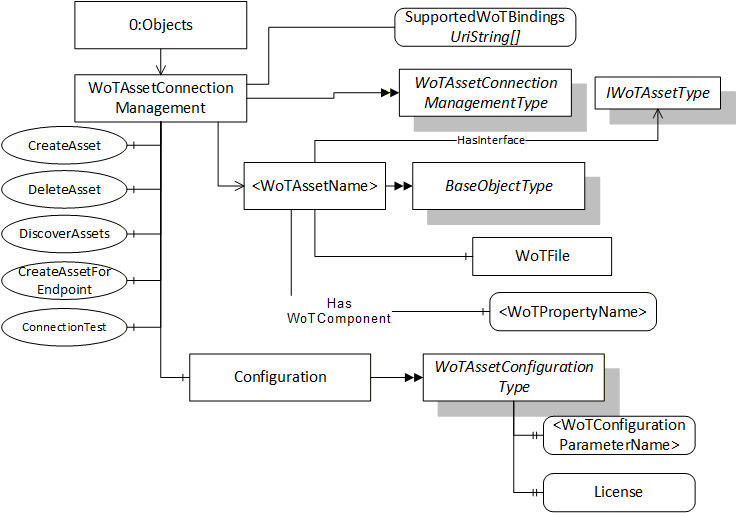
The WoTAssetConnectionManagement Node is formally defined in Table 4.
| Attribute | Value | ||
| BrowseName | WoTAssetConnectionManagement | ||
| References | NodeClass | BrowseName | |
|---|---|---|---|
| OrganizedBy by the 0:Objects Folder defined in OPC 10000-5 | |||
| 0:HasTypeDefinition | ObjectType | WoTAssetConnectionManagementType | |
| Conformance Units | |||
|---|---|---|---|
| WoT Connectivity Base Functionality |
6.3 OPC UA Information Model
6.3.1 WoTAssetConnectionManagementType
6.3.1.1 Definition
The WoTAssetConnectionManagementType ObjectType represents a set of WoTAssets that may be managed by a Server. It is defined in Table 5.
| Attribute | Value | |||||
| BrowseName | WoTAssetConnectionManagementType | |||||
| IsAbstract | False | |||||
| References | NodeClass | BrowseName | DataType | TypeDefinition | Other | |
|---|---|---|---|---|---|---|
| Subtype of the 0:BaseObjectType defined in OPC 10000-5. | ||||||
| 0:Organizes | Object | <WoTAssetName> | 0:BaseObjectType | OP | ||
| 0:HasProperty | Variable | SupportedWoTBindings | 0:UriString[] | 0:PropertyType | O | |
| 0:HasComponent | Method | CreateAsset | Defined in 6.3.2 | M | ||
| 0:HasComponent | Method | DeleteAsset | Defined in 6.3.3. | M | ||
| 0:HasComponent | Method | DiscoverAssets | Defined in 6.3.4. | O | ||
| 0:HasComponent | Method | CreateAssetForEndpoint | Defined in 6.3.5. | O | ||
| 0:HasComponent | Method | ConnectionTest | Defined in 6.3.6. | O | ||
| 0:HasComponent | Object | Configuration | Defined in 6.3.7. | WoTAssetConfigurationType | O | |
| Conformance Units | ||||||
|---|---|---|---|---|---|---|
| WoT Connectivity Base Functionality |
Any instance of the <WoTAssetName> Object shall implement the IWoTAssetType Interface.
The SupportedWoTBindings Property is a UriString Array of supported WoT protocol bindings by the Server. The currently defined WoT protocol bindings are defined in WoT Binding.
The CreateAsset Method creates a new Object that implements the IWoTAssetType Interface organized by the WoTAssetConnectionManagement Object. This method should be used when an existing WoT Thing Description file is available.
The DeleteAsset Method shall remove the Organizes Reference from the WoTAssetConnectionManagement Object and may delete the IWoTAssetType instance.
The DiscoverAssets Method shall auto-discover assets on the network satisfying the search path provided. It returns a list of endpoints to the assets discovered.
The CreateAssetForEndpoint Method browses the specified asset. It then creates a new Object that implements the IWoTAssetType Interface organized by the WoTAssetConnectionManagement Object. In addition, a WoT Thing Description file shall be automatically generated by the connectivity software and made available through the WoTAssetFileType node.
The ConnectionTest Method tests the connection to an asset on the network.
The Configuration Object is used to get or set the configuration of the industrial connectivity software.
The components of the WoTAssetConnectionManagementType have additional references which are defined in Table 6.
The flow of calling the methods to first discover an asset and then download, modify and upload a WoT file for it is the following:
User calls DiscoverAssets Method to enumerate the list of discoverable asset endpoints on the network.
Optional: User calls ConnectionTest Method to check if access to a particular discovered asset is possible at all.
User calls CreateAssetForEndpoint Method to automatically generate a WoT Thing Description (TD) file for a particular discovered asset. A new OPC UA File node is automatically added to the Server’s address below the WoTAssetConnectionManagement Node space to allow access to the generated file from a connected OPC UA client.
User calls Open Method on the File node automatically created during the previous step.
User calls Read Method to download the WoT TD file to the connected OPC UA client.
User edits the WoT TD file with additional data that may be available for the asset.
User calls CloseAndUpdate Method to parse the WoT TD file and map the asset’s tags into the Server’s address space.
User browses the new OPC UA Nodes generated during the mapping process and reads/publishes their data.
| SourceBrowsePath | Reference Type | Is Forward | TargetBrowsePath |
| <WoTAssetName> | 0:HasInterface | True | IWoTAssetType |
6.3.2 CreateAsset Method
CreateAsset creates a new Object that implements the IWoTAssetType Interface that can be used to upload the WoT TD file to the server. Once the upload is complete, the industrial asset becomes reachable via the OPC UA server. The WoT TD file fully defines the endpoint, protocol, and all asset tags to be mapped to OPC UA.
CreateAsset, when successful, returns the NodeId of the newly created Object and adds an Organizes Reference from the WoTAssetConnectionManagement Object.
Signature
CreateAsset(
[in] 0:String AssetName,
[out] 0:NodeId AssetId);| Argument | Description |
| AssetName | A unique name for the asset. |
| AssetId | The NodeId of the WoTAsset Object, if call was successful. |
Method Result Codes
| Result Code Symbolic Id | Description |
| Bad_BrowseNameDuplicated | The AssetName is already used. |
| Bad_UserAccessDenied | The session (including the user) does not have the permissions required. |
6.3.3 DeleteAsset Method
Signature
DeleteAsset(
[in] 0:NodeId AssetId);| Argument | Description |
| AssetId | The NodeId of the WoTAsset Object. |
Method Result Codes
| Result Code Symbolic Id | Description |
| Bad_NotFound | The asset was not found. |
| Bad_InvalidArgument | The NodeId provided was invalid. |
| Bad_UserAccessDenied | The session (including the user) does not have the permissions required. |
6.3.4 DiscoverAssets Method
Signature
DiscoverAssets(
[out] 0:String[] AssetEndpoints);| Argument | Description |
| AssetEndpoints | The list of discovered asset endpoints. |
Method Result Codes
| Result Code Symbolic Id | Description |
6.3.5 CreateAssetForEndpoint Method
Signature
CreateAssetForEndpoint(
[in] 0:String AssetName
[in] 0:String AssetEndpoint
[out] 0:NodeId AssetId);
| Argument | Description |
| AssetName | The name to be assigned to the asset. |
| AssetEndpoint | The endpoint to the asset on the network. |
| AssetId | The NodeId of the WoTAsset Object, if call was successful. |
Method Result Codes
| Result Code Symbolic Id | Description |
6.3.6 ConnectionTest Method
Signature
ConnectionTest(
[in] 0:String AssetEndpoint
[out] 0:Boolean Success
[out] 0:String Status);| Argument | Description |
| AssetEndpoint | The endpoint description of the asset to test the connection to. |
| Success | Returns TRUE if a connection could be established to the asset, FALSE otherwise. |
| Status | If a connection was established successfully, an asset-specific status code string describing the current health of the asset is returned. |
Method Result Codes
| Result Code Symbolic Id | Description |
| Bad_UserAccessDenied | The session (including the user) does not have the permissions required. |
| Good | A connection was established successfully. |
6.3.7 WoTAssetConfigurationType
The WoTAssetConfigurationType defines the properties of the industrial connectivity software that can be configured. The children of the WoTAssetConfigurationType are properties that can be of any name and are vendor-specific. One such property is a license string for the product.
| Attribute | Value | ||||
| BrowseName | WoTAssetConfigurationType | ||||
| IsAbstract | False | ||||
| References | NodeClass | BrowseName | DataType | TypeDefinition | Other |
|---|---|---|---|---|---|
| Subtype of the 0:BaseInterfaceType defined in OPC 10000-5. | |||||
| 0:HasProperty | Variable | <WoTConfigurationParameterName> | 0:BaseDataType | 0:PropertyType | OP |
| 0:HasProperty | Variable | License | 0:String | 0:PropertyType | O |
| Conformance Units | |||||
|---|---|---|---|---|---|
| WoT Connectivity Base Functionality |
6.3.8 IWoTAssetType
The IWoTAssetType is an Interface representing the WoT asset functionality. It has a component representing a File Object that can be used to upload the WoT TD file. It is defined in Table 13.
| Attribute | Value | ||||
| BrowseName | IWoTAssetType | ||||
| IsAbstract | True | ||||
| References | NodeClass | BrowseName | DataType | TypeDefinition | Other |
|---|---|---|---|---|---|
| Subtype of the 0:BaseInterfaceType defined in OPC 10000-5. | |||||
| 1:HasWoTComponent | Variable | <WoTPropertyName> | 0:BaseDataType | 0:BaseDataVariableType | OP |
| 0:HasProperty | Variable | AssetEndpoint | 0:String | 0:PropertyType | O |
| 0:HasComponent | Object | WoTFile | WoTAssetFileType | M | |
| Conformance Units | |||||
|---|---|---|---|---|---|
| WoT Connectivity Base Functionality |
When the asset configuration is complete, the Server may update the internal configuration of existing Variable Nodes or it may add new Variable Nodes to represent the asset. Each WoT property in the forms section of the TD shall have exactly one VariableNode associated with it.
The WoTAsset Object must have hierarchical HasWoTComponent references to the newly created Variable Nodes, one for each WoT property. The BrowseName of the Variable Node shall have a name equal to the WoT property name. The namespace used is server-specific.
The AssetEndpoint Property contains the endpoint where the asset can be found on the network. The syntax of the endpoint is vendor-specific.
If a mapping to a WoT property cannot be done (e.g. the data cannot be read from the connected asset), the built-in status code Bad_ConfigurationError will be returned when the Value of the Variable is read.
Each WoT property type is mapped to the corresponding OPC UA built-in DataType using the following mapping table:
| WoT Property Type | OPC UA Data Type |
| Boolean | Boolean |
| Number | Double |
| Integer | Int64 |
| Object | No mapping |
| String | String |
| Null | No mapping |
| array[Items] | Array[of one of above defined types] |
6.3.9 WoT Actions Mapping
WoT Actions are represented as Method Node which is component of an Object that implements IWoTAssetType (see 6.3.8). The Method and its InputArguments and OutputArguments Properties are mapped to a TD as shown in Table 15.
| WoT Field | OPC UA Method Mapping |
| uav:BrowseName | BrowseName |
| Title | DisplayName |
| uav:ComponentOf | ComponentOf Reference Target NodeId |
| Input.Title | InputArguments.Description |
| Input.Properties | InputArguments.Value |
| Output.Title | OutputArguments.Description |
| Output.Properties | OutputArguments.Value |
| Forms.Href | NodeId |
"actions": {
"setTemperature": {
"title": "Set Temperature",
"description": "Sets the desired temperature",
"input": {
"type": "object",
"title": "SetTemperature",
"properties": {
"target": {
"type": "number",
"minimum": 10,
"maximum": 30,
"unit": "degree Celsius"
}
}
}
"forms": [
{
"href": "https://example.com/things/thermostat/actions/setTemperature",
"contentType": "application/json",
"htv:methodName": "POST"
}
]
}
}
{ "target": 22.5 }6.3.10 WoTAssetFileType
6.3.10.1 Definition
The WoTAssetFileType ObjectType represents a TD File that is used to define an WoTAsset. It is defined in Table 16.
All instances shall support a mode of Write + EraseExisting when Open is called. They may support mode of Read. Other modes are not allowed.
When writing, if Close is called the file is discard and nothing changes. If CloseAndUpdate is called the file is parsed and the variables are updated to match the WoT TD file.
| Attribute | Value | ||||
| BrowseName | WoTAssetFileType | ||||
| IsAbstract | False | ||||
| References | NodeClass | BrowseName | DataType | TypeDefinition | Modelling Rule |
|---|---|---|---|---|---|
| Subtype of the 0:FileType defined in OPC 10000-5. | |||||
| 0:HasComponent | Method | CloseAndUpdate | Defined in 6.3.10.2 | Mandatory | |
| Conformance Units | |||||
|---|---|---|---|---|---|
| WoT Connectivity Base Functionality |
The CloseAndUpdate Method parses the TD and creates Variables from the TD properties.
6.3.10.2 CloseAndUpdate Method
Signature
CloseAndUpdate (
[in] 0:UInt32 FileHandle);| Argument | Description |
| FileHandle | The handle for a file opened for writing. |
Method Result Codes
| Result Code Symbolic Id | Description |
| Bad_InvalidState | The file was not opened for writing. |
| Bad_DecodingError | The WoT Thing Description could not be parsed. |
| Bad_NotSupported | The TD is valid but cannot be mapped to OPC UA. |
| Bad_NotFound | The asset was not found on the network |
| Bad_UserAccessDenied | The session does not have the permissions required. |
6.3.11 HasWoTComponent ReferenceType
The HasWoTComponent is a concrete ReferenceType used to link WoT asset Objects to the WoT properties. The source node shall be an instance of an Object implementing the IWoTAssetType Interface. The target Node shall be an instance or a subtype of a BaseDataVariableType.
The HasWoTComponent representation in the AddressSpace is specified in Table 18.
| Attributes | Value | ||
| BrowseName | HasWoTComponent | ||
| InverseName | WoTComponentOf | ||
| Symmetric | False | ||
| IsAbstract | False | ||
| References | NodeClass | BrowseName | Comment |
|---|---|---|---|
| Subtype of 0:HasComponent ReferenceType defined in OPC 10000-5. | |||
| Conformance Units | |||
| WoT Connectivity Base Functionality | |||
7 Profiles and Conformance Units
Meaning and significance of Profiles and ConformanceUnits are described in OPC 10000-7.
The Profiles and ConformanceUnits for this specification are maintained in the online database and accessible via https://profiles.opcfoundation.org/?pg=WoTConnectivity%201.0x.
8 Namespaces
8.1 Namespace Metadata
Table 19 defines the namespace metadata for this document. The Object is used to provide version information for the namespace and an indication about static Nodes. Static Nodes are identical for all Attributes in all Servers, including the Value Attribute. See OPC 10000-5 for more details.
The information is provided as Object of type NamespaceMetadataType. This Object is a component of the Namespaces Object that is part of the Server Object. The NamespaceMetadataType ObjectType and its Properties are defined in OPC 10000-5.
The version information is also provided as part of the ModelTableEntry in the UANodeSet XML file. The UANodeSet XML schema is defined in OPC 10000-6.
| Attribute | Value | ||
| BrowseName | http://opcfoundation.org/UA/WoT-Con/ | ||
| Property | DataType | Value | |
|---|---|---|---|
| NamespaceUri | String | http://opcfoundation.org/UA/WoT-Con/ | |
| NamespaceVersion | String | 1.02.0 | |
| NamespacePublicationDate | DateTime | 2025-12-05 | |
| IsNamespaceSubset | Boolean | False | |
| StaticNodeIdTypes | IdType[] | 0 | |
| StaticNumericNodeIdRange | NumericRange [] | ||
| StaticStringNodeIdPattern | String | ||
Note: The IsNamespaceSubset Property is set to False as the UA Nodeset XML file contains the complete Namespace. Servers only exposing a subset of the Namespace need to change the value to True.
8.2 Handling of OPC UA Namespaces
Namespaces are used by OPC UA to create unique identifiers across different naming authorities. The Attributes NodeId and BrowseName are identifiers. A Node in the UA AddressSpace is unambiguously identified using a NodeId. Unlike NodeIds, the BrowseName cannot be used to unambiguously identify a Node. Different Nodes may have the same BrowseName. They are used to build a browse path between two Nodes or to define a standard Property.
Servers may often choose to use the same namespace for the NodeId and the BrowseName. However, if they want to provide a standard Property, its BrowseName shall have the namespace of the standards body although the namespace of the NodeId reflects something else, for example the EngineeringUnits Property. All NodeIds of Nodes not defined in this document shall not use the standard namespaces.
Table 20 provides a list of namespaces typically used in a Web of Things OPC UA Server.
| NamespaceURI | Description |
| http://opcfoundation.org/UA/ | Namespace for NodeIds and BrowseNames defined in the OPC UA specification. This namespace shall have namespace index 0. |
| Local Server URI | Namespace for nodes defined in the local server. This namespace shall have namespace index 1. |
| http://opcfoundation.org/UA/WoT-Con/ | Namespace for NodeIds and BrowseNames defined in this document. The namespace index is Server specific. |
| Vendor specific types | A Server may provide vendor-specific types like types derived from ObjectTypes defined in this document in a vendor-specific namespace. |
| Vendor specific instances | A Server provides vendor-specific instances of the standard types or vendor-specific instances of vendor-specific types in a vendor-specific namespace. It is recommended to separate vendor specific types and vendor specific instances into two or more namespaces. |
Table 21 provides a list of namespaces and their indices used for BrowseNames in this document. The default namespace of this document is not listed since all BrowseNames without prefix use this default namespace.
The three OPC UA methods defined in the previous section shall be mapped into the namespace defined in this section.
| NamespaceURI | Namespace Index | Example |
| http://opcfoundation.org/UA/ | 0 | 0:EngineeringUnits |
Annex A WoT Connectivity Namespace and mappings (Normative)
A.1 NodeSet and supplementary files for WoT Connectivity Information Model
The WoT Connectivity Information Model is identified by the following URI:
http://opcfoundation.org/UA/WoT-Con/
Documentation for the NamespaceUri can be found here.
The NodeSet associated with this version of specification can be found here:
https://reference.opcfoundation.org/nodesets/?u=http://opcfoundation.org/UA/WoT-Con/&v=1.02.0&i=1
The NodeSet associated with the latest version of the specification can be found here:
https://reference.opcfoundation.org/nodesets/?u=http://opcfoundation.org/UA/WoT-Con/&i=1
Supplementary files for the WoT Connectivity Information Model can be found here:
https://reference.opcfoundation.org/nodesets/?u=http://opcfoundation.org/UA/WoT-Con/&v=1.02.0&i=2
The files associated with the latest version of the specification can be found here:
https://reference.opcfoundation.org/nodesets/?u=http://opcfoundation.org/UA/WoT-Con/&i=2
A.2 WoT Connectivity Thing Description JSON Schema
The WoT Connectivity Thing Description JSON schema can be found here:
https://github.com/w3c/wot-thing-description/blob/main/validation/td-json-schema-validation.json
Annex B (non-normative) WoT Thing Description Tools
For Web of Things Thing Description editing and schema validation, please refer to the open-source Eclipse Foundation ediTDor here: https://eclipse.github.io/editdor
For Web of Things Thing Description non-interactive validation, please refer to the open-source Eclipse Foundation Thing Description Playground here:
https://github.com/eclipse-thingweb/playground
________
Agreement of Use
COPYRIGHT RESTRICTIONS
This document is provided "as is" by the OPC Foundation.
Right of use for this specification is restricted to this specification and does not grant rights of use for referred documents.
Right of use for this specification will be granted without cost.
This document may be distributed through computer systems, printed or copied as long as the content remains unchanged and the document is not modified.
OPC Foundation does not guarantee usability for any purpose and shall not be made liable for any case using the content of this document.
The user of the document agrees to indemnify OPC Foundation and their officers, directors and agents harmless from all demands, claims, actions, losses, damages (including damages from personal injuries), costs and expenses (including attorneys' fees) which are in any way related to activities associated with its use of content from this specification.
The document shall not be used in conjunction with company advertising, shall not be sold or licensed to any party.
The intellectual property and copyright is solely owned by the OPC Foundation.
OPC Foundation members and any non-members are prohibited from copying and redistributing this specification. All copies must be obtained on an individual basis, directly from the OPC Foundation Web site http://www.opcfoundation.org.
PATENTS
The attention of adopters is directed to the possibility that compliance with or adoption of OPC specifications may require use of an invention covered by patent rights. OPC shall not be responsible for identifying patents for which a license may be required by any OPC specification, or for conducting legal inquiries into the legal validity or scope of those patents that are brought to its attention. OPC specifications are prospective and advisory only. Prospective users are responsible for protecting themselves against liability for infringement of patents.
WARRANTY AND LIABILITY DISCLAIMERS
WHILE THIS PUBLICATION IS BELIEVED TO BE ACCURATE, IT IS PROVIDED "AS IS" AND MAY CONTAIN ERRORS OR MISPRINTS. THE OPC FOUDATION MAKES NO WARRANTY OF ANY KIND, EXPRESSED OR IMPLIED, WITH REGARD TO THIS PUBLICATION, INCLUDING BUT NOT LIMITED TO ANY WARRANTY OF TITLE OR OWNERSHIP, IMPLIED WARRANTY OF MERCHANTABILITY OR WARRANTY OF FITNESS FOR A PARTICULAR PURPOSE OR USE. IN NO EVENT SHALL THE OPC FOUNDATION BE LIABLE FOR ERRORS CONTAINED HEREIN OR FOR DIRECT, INDIRECT, INCIDENTAL, SPECIAL, CONSEQUENTIAL, RELIANCE OR COVER DAMAGES, INCLUDING LOSS OF PROFITS, REVENUE, DATA OR USE, INCURRED BY ANY USER OR ANY THIRD PARTY IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS MATERIAL, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
The entire risk as to the quality and performance of software developed using this specification is borne by you.
RESTRICTED RIGHTS LEGEND
This Specification is provided with Restricted Rights. Use, duplication or disclosure by the U.S. government is subject to restrictions as set forth in (a) this Agreement pursuant to DFARs 227.7202-3(a); (b) subparagraph (c)(1)(i) of the Rights in Technical Data and Computer Software clause at DFARs 252.227-7013; or (c) the Commercial Computer Software Restricted Rights clause at FAR 52.227-19 subdivision (c)(1) and (2), as applicable. Contractor / manufacturer is the OPC Foundation, 16101 N. 82nd Street, Suite 3B, Scottsdale, AZ, 85260-1830.
COMPLIANCE
The OPC Foundation shall at all times be the only entities that may authorize developers, suppliers and sellers of hardware and software to use certification marks, trademarks or other special designations to indicate compliance with these materials. Products developed using this specification may claim compliance or conformance with this specification if and only if the software satisfactorily meets the certification requirements set by the OPC Foundation. Products that do not meet these requirements may claim only that the product was based on this specification and must not claim compliance or conformance with this specification.
TRADEMARKS
Most computer and software brand names have trademarks or registered trademarks. The individual trademarks have not been listed here.
GENERAL PROVISIONS
Should any provision of this Agreement be held to be void, invalid, unenforceable or illegal by a court, the validity and enforceability of the other provisions shall not be affected thereby.
This Agreement shall be governed by and construed under the laws of the State of Minnesota, excluding its choice or law rules.
This Agreement embodies the entire understanding between the parties with respect to, and supersedes any prior understanding or agreement (oral or written) relating to, this specification.
ISSUE REPORTING
If an error or problem is found in this specification, the UaNodeSet, or any associated supplementary files, it should be reported as an issue.
The reporting process can be found here: https://opcfoundation.org/resources/issue-tracking/
The Link to the issue tracking project for this document is here:
https://mantis.opcfoundation.org/set_project.php?project_id=227&make_default=no
