9 AuthorizationServices
9.1 Overview
AuthorizationServices provide AccessTokens to Clients that may use them to access resources. A Server, such as a GDS, with AuthorizationService Capabilities may support one or more AuthorizationService Objects (see 9.6.4) which may represent an internal AuthorizationService or be an API to an external AuthorizationService. The AuthorizationService is best used in conjunction with the Role model defined in OPC 10000-5. In this scenario, the mapping rules assigned to the Roles known to the Server are used to populate an AccessToken with the Roles associated with the UserIdentity provided when the Client submits the request. This scenario is illustrated in Figure 29.
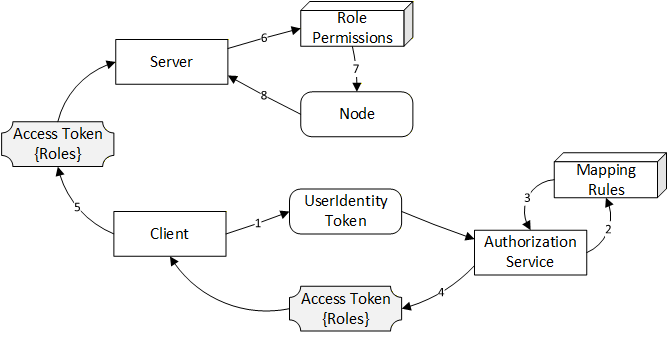
When requesting AccessTokens from an AuthorizationService Object there are three primary use cases based on where the UserIdentityToken comes from: Implicit, Explicit and Chained. These use cases are discussed below. The Implicit and Explicit use cases are implementations of the ‘Indirect’ model for AuthorizationServices described in OPC 10000-4. The Chained use case is an implementation of the ‘Direct’ model.
9.2 Roles and Privileges
AuthorizationServices restrict access to many of the features they provide. These restrictions are described either by referring to well-known Roles which a Session must have access to or by referring to Privileges which are assigned to Sessions using mechanisms other than the well-known Roles. The well-known Roles for an AuthorizationService are listed in Table 142.
| Name | Description |
|---|---|
| AuthorizationServiceAdmin | This Role grants the right to manage the configuration of an AuthorizationService. |
| SecurityAdmin | This Role grants the right to change the security configuration of an AuthorizationService. |
The Privileges for an AuthorizationService are listed in Table 143.
| Name | Description |
|---|---|
| AccessTokenRequestor | This Privilege grants an OPC UA Application the right to request AccessTokens. The Certificate used to create the SecureChannel is used to determine the identity of the OPC UA Application. A KeyCredential (see 8) provided as a UserIdentityToken may also be used to determine if the Client has access to this Privilege. |
9.3 Implicit
The implicit authorization use case describes how the Client’s ApplicationInstance Certificate and any UserIdentityToken associated with the Session is used to determine whether an AccessToken is permitted and what claims are available. This use case is illustrated in Figure 30.
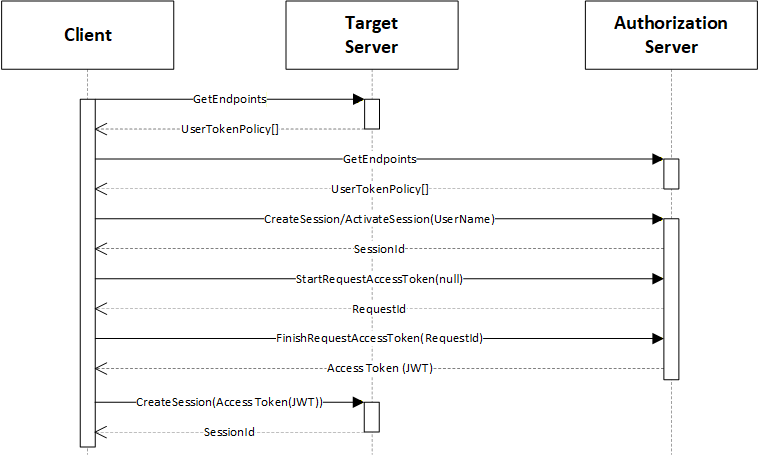
The "Target Server" is the Server that the Client wishes to access. It publishes a UserTokenPolicy that indicates that it accepts AccessTokens from an "Authorization Server". The parameters needed to connect to the "Authorization Server" are stored in the IssuerEndpointUrl field of the UserTokenPolicy and are defined in OPC 10000-6. These parameters are specified as a JSON object rather than a URL as implied by the field name and requirements specific to AuthorizationServices are defined in Table 144.
| Name | Description |
|---|---|
IssuerEndpointUrl ua:authorityUrl | The URL of the "Authorization Server". |
IssuerEndpointUrl ua:tokenEndpoint | The NodeId of the AuthorizationService Object encoded using the URI qualified syntax defined in OPC 10000-6. |
IssuerEndpointUrl ua:authorizationEndpoint | The NodeId of the UserTokenPolicies Property. Shall be null if Implicit Authorization is required. Shall be non-null if Explicit Authorization is required (see 9.4). |
The Client shall be trusted by the "Authorization Server" and could require the Client to present user credentials. These credentials can be provided to the Client out-of-band (e.g. an administrator specified them in the Client configuration file). The user credentials used can be any type of user credential including X.509 and JWT.
The Session with the "Authorization Server" may be created explicitly with a call to CreateSession or it can be implicit via a Session-less Method Call.
With this use case, the Client uses the EndpointDescriptions provided by the "Authorization Server" to determine what credentials to provide when creating a Session.
The Client then calls the StartRequestToken and FinishRequestToken Methods on the AuthorizationService Object. The "Authorization Server" determines if the Client is permitted to receive an AccessToken and populates it with any claims granted to the Client.
The AccessToken includes a list of network Roles granted to the Client. The network Roles are abstract Roles defined by the system administrator that are mapped onto the Roles supported by each Target Server with IdentityMappingRules set by the administrator (see OPC 10000-18).
Once the Client has the AccessToken, it passes the AccessToken to the Target Server which validates the AccessToken, as described in OPC 10000-4. The Target Server is configured out-of-band with the Certificate used to validate the AccessTokens issued by the Authorization Server.
9.4 Explicit
The explicit authorization use case describes how a Client authenticates itself with a UserIdentityToken provided in the FinishRequestToken Method call. User credentials for Session with the Authorization Server are not required. This use case is illustrated in Figure 31.
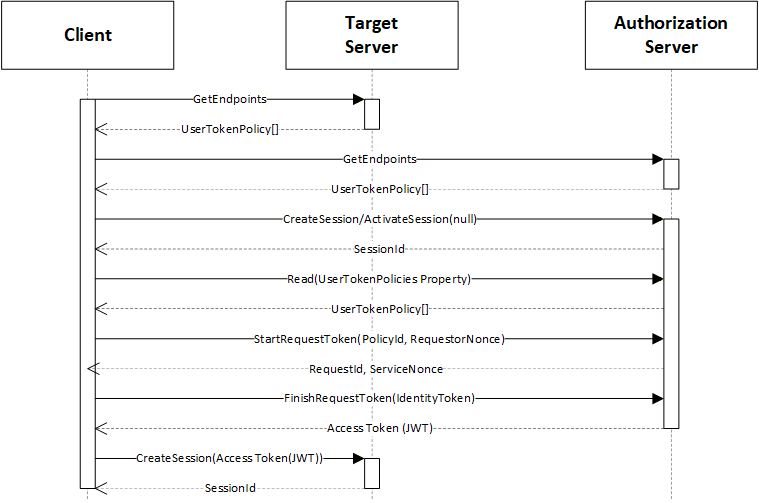
The "Target Server" is the Server that the Client wishes to access. It publishes a UserTokenPolicy that indicates that it accepts AccessTokens from an "Authorization Server". The parameters needed to connect to the "Authorization Server" are stored in the UserTokenPolicy (see Table 144).
With this use case, the Client reads the UserTokenPolicies Property of the AuthorizationService by reading the value of the UserTokenPolicies Property. The NodeId of UserTokenPolicies Property is provided in the UserTokenPolicy provided by the Target Server (see Table 144).
The Client then calls the StartRequestToken and FinishRequestToken Methods on the AuthorizationService Object. The "Authorization Server" determines if the Client is permitted to receive an AccessToken and populates it with any claims granted to the Client. The StartRequestToken and FinishRequestToken Methods can be invoked via Session-less Method calls.
9.5 Chained
The chained authorization use case is a variation on the explicit authorization use case, where the UserIdentityToken provided to the "Authorization Server" is an AccessToken issued by an "Identity Provider". This is useful in systems where the IT infrastructure manages authentication of users, however, the "Authorization Server" is needed to map the IT users onto system specific Roles.
This use case is illustrated in Figure 32.
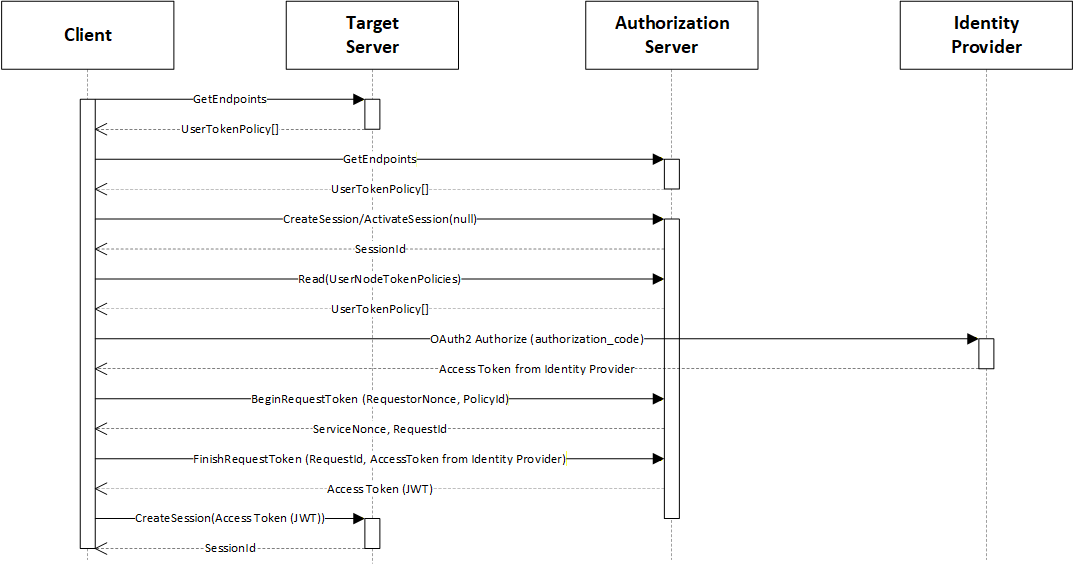
The "Target Server" is the Server that the Client wishes to access. The interactions are the same as with the Explicit authorization use case described in 9.3 except a call to the "Identity Service" is inserted before the Client calls the StartRequestToken Method.
9.6 Information Model for Requesting AccessTokens
9.6.1 Overview
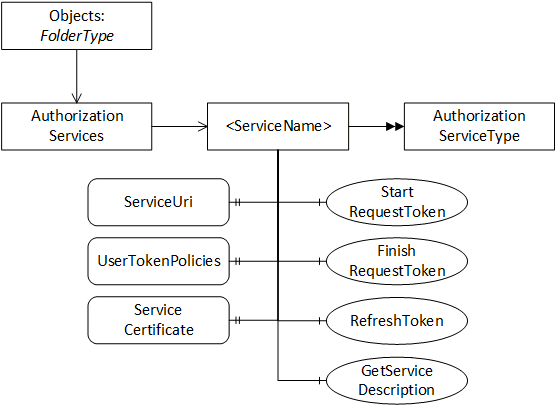
The information model for AuthorizationServices which allow Clients to request AccessTokens from a Server is shown in Figure 33.
9.6.2 AuthorizationServicesFolderType
This ObjectType represents a folder that contains AuthorizationService Objects which may be accessed via the Server. It is defined in Table 145.
| Attribute | Value | |||
| BrowseName | 2:AuthorizationServicesFolderType | |||
| IsAbstract | False | |||
| References | NodeClass | BrowseName | TypeDefinition | Modelling Rule |
|---|---|---|---|---|
| Subtype of the FolderType defined in OPC 10000-5. | ||||
| 0:Organizes | Object | 2:<ServiceName> | 2:AuthorizationServiceType | OptionalPlaceholder |
| Conformance Units | ||||
|---|---|---|---|---|
| GDS Authorization Service Server |
9.6.3 AuthorizationServices
This Object is an instance of AuthorizationServicesFolderType. It contains the AuthorizationService Objects which may be accessed via the GDS. It is the target of an Organizes reference from the Objects Folder defined in OPC 10000-5. It is defined in Table 146.
| Attribute | Value | |||
| BrowseName | 2:AuthorizationServices | |||
| TypeDefinition | 2:AuthorizationServicesFolderType defined in 9.6.2. | |||
| References | NodeClass | BrowseName | TypeDefinition | Modelling Rule |
|---|---|---|---|---|
| Conformance Units | ||||
|---|---|---|---|---|
| GDS Authorization Service Server |
9.6.4 AuthorizationServiceType
This ObjectType is the TypeDefinition for an Object that allows access to an AuthorizationService. It is defined in Table 147.
| Attribute | Value | ||||
| BrowseName | 2:AuthorizationServiceType | ||||
| IsAbstract | False | ||||
| References | NodeClass | BrowseName | DataType | TypeDefinition | Modelling Rule |
|---|---|---|---|---|---|
| Subtype of the BaseObjectType defined in OPC 10000-5. | |||||
| 0:HasProperty | Variable | 2:ServiceUri | 0:String | 0:PropertyType | Mandatory |
| 0:HasProperty | Variable | 2:ServiceCertificate | 0:ByteString | 0:PropertyType | Mandatory |
| 0:HasProperty | Variable | 2:UserTokenPolicies | 0:UserTokenPolicy [] | 0:PropertyType | Optional |
| 0:HasProperty | Variable | 2:SupportedRoles | 0:String[] | 0:PropertyType | Optional |
| 0:HasComponent | Method | 2:RequestAccessToken | Defined in 9.6.5. | Optional | |
| 0:HasComponent | Method | 2:StartRequestToken | Defined in 9.6.6. | Optional | |
| 0:HasComponent | Method | 2:FinishRequestToken | Defined in 9.6.7. | Optional | |
| 0:HasComponent | Method | 2:RefreshToken | Defined in 9.6.8. | Optional | |
| 0:HasComponent | Method | 2:GetServiceDescription | Defined in 9.6.9. | Mandatory | |
| 0:GeneratesEvent | ObjectType | 2:AccessTokenRequestedAuditEventType | Defined in 9.6.10. | ||
| 0:GeneratesEvent | ObjectType | 2:AccessTokenIssuedAuditEventType | Defined in 9.6.11. | ||
| Conformance Units | |||||
|---|---|---|---|---|---|
| GDS Authorization Service Server |
The ServiceUri Property contains a globally unique identifier that allows a Client to correlate an instance of AuthorizationServiceType with instances of AuthorizationServiceConfigurationType (see 9.7.4).
The ServiceCertificate Property contains the Certificate required to check any Signature that is included with the AccessTokens. The ServiceCertificate may be a complete chain (see OPC 10000-6 for information on encoding chains). CRLs are not used by the target Server when verifying AccessTokens. It is the responsibility of the AuthorizationService to verify that the ServiceCertificate is not revoked or otherwise invalid before returning any AccessToken to Clients. When a CertificateManager pushes the configuration to a target Server, the CertificateManager is responsible for verifying the ServiceCertificate and automatically updating the target Server if the ServiceCertificate is revoked.
The UserTokenPolicies Property specifies the UserIdentityTokens which are accepted by the RequestAccessToken or FinishRequestToken Methods.
The SupportedRoles Property specifies the system-wide Roles which may be included in an AccessToken. Each target Server uses mapping rules (see OPC 10000-18) to specify the relationship between the system-wide Roles and Roles known to the target Server.
The GetServiceDescription Method is used to read the metadata used to request AccessTokens.
The RequestAccessToken Method is used to request an AccessToken from the AuthorizationService.
The StartRequestToken Method initiates a request for an AccessToken from the AuthorizationService.
The FinishRequestToken Method completes a request for an AccessToken from the AuthorizationService.
The RefreshToken Method is used to request an updated AccessToken.
9.6.5 RequestAccessToken (Deprecated)
It is deprecated because it can only be used with unencrypted UserName IdentityTokens. Use StartRequestToken instead.
RequestAccessToken is used to request an AccessToken from an AuthorizationService. The scenarios where this Method is used are described fully in 9.3, 9.4 and 9.5.
The PolicyId and UserTokenType of the IdentityToken shall match one of the elements of the UserTokenPolicies Property. If the IdentityToken is not provided the Server should use the ApplicationInstanceCertificate and/or the UserIdentityToken provided for the Session (or the request if using a Session-less Method Call) to determine privileges.
If the associated UserTokenPolicy provides a SecurityPolicyUri, then the IdentityToken is encrypted and digitally signed using the format defined for UserIdentityToken secrets in OPC 10000-4.
This Method shall be called from an encrypted SecureChannel and from a Client that has access to the AccessTokenRequestor Privilege (see 9.2).
Signature
RequestAccessToken (
[in] UserIdentityToken IdentityToken
[in] String ResourceId
[out] String AccessToken
);| Argument | Description |
| IdentityToken | The identity used to authorize the AccessToken request. |
| ResourceId | The identifier for the Resource that the AccessToken is used to access. This is usually the ApplicationUri for a Server. The recommended source of this value is the ResourceId in the UserTokenPolicy provided by the Server that the caller wants to connect to (see OPC 10000-6). |
| AccessToken | The AccessToken granted to the application. |
Method Result Codes (defined in Call Service)
| Result Code | Description |
| Bad_IdentityTokenInvalid | The IdentityToken does not match one of the allowed UserTokenPolicies. |
| Bad_IdentityTokenRejected | The IdentityToken was rejected. |
| Bad_NotFound | The ResourceId is not known to the Server. |
| Bad_UserAccessDenied | The current user does not have the rights required. |
| Bad_SecurityModeInsufficient | The SecureChannel is not encrypted. |
Table 148 specifies the AddressSpace representation for the RequestAccessToken Method.
| Attribute | Value | ||||
| BrowseName | 2:RequestAccessToken | ||||
| References | NodeClass | BrowseName | DataType | TypeDefinition | ModellingRule |
|---|---|---|---|---|---|
| 0:HasProperty | Variable | 0:InputArguments | 0:Argument[] | 0:PropertyType | Mandatory |
| 0:HasProperty | Variable | 0:OutputArguments | 0:Argument[] | 0:PropertyType | Mandatory |
9.6.6 StartRequestToken
The StartRequestToken Method is used to initiate a new request for an AccessToken.
The PolicyId provided shall identify one of the UserTokenPolicies for the AuthorizationService Object.
The contents of the RequestorData and ServiceData depend on the UserTokenType and the SecurityPolicy. Table 149 specifies the contents for different combinations of UserTokenType and SecurityPolicy.
| UserTokenType | RequestorData | ServiceData |
|---|---|---|
UserName or IssuedToken SecurityPolicy: None | Not Used | Not Used |
UserName or IssuedToken SecurityPolicy: RSA | Not Used | A Certificate containing the PublicKey used to build the RsaEncryptedSecret defined in OPC 10000-4. |
UserName or IssuedToken SecurityPolicy: ECC or RSA_DH. | Not Used | An EphemeralKey used to build the EccEncryptedSecret defined in OPC 10000-4. |
| Certificate | A cryptographically random value generated by the requestor. | A cryptographically random value generated by the service. |
The AuthorizationService cleans up unused requestIds. Client should call FinishRequestToken immediately after this Method returns. The RequestId is only accessible via the current Session and resources are freed when the Session is closed.
This Method shall be called from an encrypted SecureChannel and from a Client that has access to the AccessTokenRequestor Privilege (see 9.2).
Signature
StartRequestToken(
[in] String ResourceId
[in] String PolicyId
[in] ByteString RequestorData
[out] ByteString ServiceData
[out] Guid RequestId
);| Argument | Description |
| ResourceId | The identifier for the Resource that the AccessToken is used to access. This is usually the ApplicationUri for a Server. Shall be the ResourceId specified in the UserTokenPolicy. This is usually the Server ApplicationUri. |
| PolicyId | The PolicyId from an element in the UserTokenPolicies array. |
| RequestorData | A value with contents described in Table 149. |
| ServiceData | A value with contents described in Table 149. |
| RequestId | A unique value for the request that is passed to FinishRequestToken. |
Method Result Codes (defined in Call Service)
| Result Code | Description |
| Bad_NotFound | The ResourceId is not known to the Server. |
| Bad_IdentityTokenInvalid | The PolicyId does not match one of the allowed UserTokenPolicies. |
| Bad_NonceInvalid | The RequestorData is not valid for the specified UserTokenPolicy. |
| Bad_UserAccessDenied | The current user does not have the rights required. |
| Bad_SecurityModeInsufficient | The SecureChannel is not encrypted. |
Table 150 specifies the AddressSpace representation for the StartRequestToken Method.
| Attribute | Value | ||||
| BrowseName | 2:StartRequestToken | ||||
| References | NodeClass | BrowseName | DataType | TypeDefinition | ModellingRule |
|---|---|---|---|---|---|
| 0:HasProperty | Variable | 0:InputArguments | 0:Argument[] | 0:PropertyType | Mandatory |
| 0:HasProperty | Variable | 0:OutputArguments | 0:Argument[] | 0:PropertyType | Mandatory |
9.6.7 FinishRequestToken
The FinishRequestToken Method is used to complete a request for an AccessToken from an AuthorizationService. It is called after calling StartRequestToken defined in 9.6.6.
The RequestedRoles are used to restrict the permissions that are granted to the AccessToken. If RequestedRoles are not provided the AuthorizationService includes all Roles available to the UserIdentityToken provided in the call. The SupportedRoles Property provides all Roles supported by the AuthorizationService.
The UserIdentityToken contains the credentials that the AccessToken will represent.
The UserTokenSignature is computed using the channel bound signatures defined in OPC 10000-4 where the ServiceData replaces the ServerNonce and the RequestorData replaces the ClientNonce.
This Method shall be called from an encrypted SecureChannel and from a Client that has access to the AccessTokenRequestor Privilege (see 9.2).
Signature
FinishRequestToken (
[in] Guid RequestId
[in] String[] RequestedRoles
[in] UserIdentityToken UserIdentityToken
[in] SignatureData UserTokenSignature
[out] String AccessToken
[out] DateTime AccessTokenExpiryTime
[out] String RefreshToken
[out] DateTime RefreshTokenExpiryTime
);| Argument | Description |
| RequestId | The identifier returned by StartRequestToken. |
| RequestedRoles | The list of Roles from the SupportedRoles Property that the requestor wants access to. If none are specified then all available Roles are granted. |
| UserIdentityToken | The identity used to authorize the AccessToken request. |
| UserTokenSignature | The Signature used to prove possession of a Certificate provided with an X509IdentityToken AccessToken. Otherwise, the parameter is null. |
| AccessToken | The AccessToken granted to the application. |
| AccessTokenExpiryTime | When the AccessToken expires. If the ExpiryTime is not known the AuthorizationServer shall provide a suitable non-null value. |
| RefreshToken | A token that can be cached and used to request a new AccessToken. |
| RefreshTokenExpiryTime | When the RefreshToken expires. If the ExpiryTime is not known the AuthorizationServer shall provide a suitable non-null value. |
Method Result Codes (defined in Call Service)
| Result Code | Description |
| Bad_NotFound | The RequestId is invalid or has expired. |
| Bad_IdentityTokenInvalid | The IdentityToken does not match one of the allowed UserTokenPolicies. |
| Bad_IdentityTokenRejected | The IdentityToken was rejected. |
| Bad_UserAccessDenied | The current user does not have the rights required. |
| Bad_SecurityModeInsufficient | The SecureChannel is not encrypted. |
Table 148 specifies the AddressSpace representation for the FinishRequestToken Method.
| Attribute | Value | ||||
| BrowseName | 2:FinishRequestToken | ||||
| References | NodeClass | BrowseName | DataType | TypeDefinition | ModellingRule |
|---|---|---|---|---|---|
| 0:HasProperty | Variable | 0:InputArguments | 0:Argument[] | 0:PropertyType | Mandatory |
| 0:HasProperty | Variable | 0:OutputArguments | 0:Argument[] | 0:PropertyType | Mandatory |
9.6.8 RefreshToken
The RefreshToken Method is used to request an AccessToken from an AuthorizationService using a cached RefreshToken.
The CurrentRefreshToken shall only be accepted if the ClientCertificate used to create the SecureChannel is the same as the ClientCertificate used when the FinishRequestToken Method returned the original RefeshToken.
This Method shall be called from an encrypted SecureChannel and from a Client that has access to the AccessTokenRequestor Privilege (see 9.2).
Signature
RefreshToken (
[in] String ResourceId
[in] String CurrentRefreshToken
[out] String AccessToken
[out] DateTime AccessTokenExpiryTime
[out] String NewRefreshToken
[out] DateTime NewRefreshTokenExpiryTime
);| Argument | Description |
| ResourceId | The identifier for the Resource that the AccessToken is used to access. This is usually the ApplicationUri for a Server. |
| CurrentRefreshToken | The RefreshToken previously returned by the AuthorizationService. |
| AccessToken | The AccessToken granted to the application. |
| AccessTokenExpiryTime | When the AccessToken expires. If the ExpiryTime is not known the AuthorizationServer shall provide a suitable non-null value. |
| NewRefreshToken | A token that can be cached and used to request a new AccessToken. It replaces the RefreshToken that was provided in the Request. If null or empty the current RefreshToken can be used again. |
| NewRefreshTokenExpiryTime | When the RefreshToken expires. If the ExpiryTime is not known the AuthorizationServer shall provide a suitable non-null value. |
Method Result Codes (defined in Call Service)
| Result Code | Description |
| Bad_IdentityTokenRejected | The RefreshToken was rejected. |
| Bad_NotFound | The ResourceId is not known to the Server. |
| Bad_UserAccessDenied | The current user does not have the rights required. |
| Bad_SecurityModeInsufficient | The SecureChannel is not encrypted. |
Table 148 specifies the AddressSpace representation for the RequestAccessToken Method.
| Attribute | Value | ||||
| BrowseName | 2:RefreshToken | ||||
| References | NodeClass | BrowseName | DataType | TypeDefinition | ModellingRule |
|---|---|---|---|---|---|
| 0:HasProperty | Variable | 0:InputArguments | 0:Argument[] | 0:PropertyType | Mandatory |
| 0:HasProperty | Variable | 0:OutputArguments | 0:Argument[] | 0:PropertyType | Mandatory |
9.6.9 GetServiceDescription
The GetServiceDescription Method is used to read the metadata needed to request AccessTokens from the AuthorizationService.
Signature
GetServiceDescription (
[out] String ServiceUri
[out] ByteString ServiceCertificate
[out] UserTokenPolicy[] UserTokenPolicies
);| Argument | Description |
| ServiceUri | A globally unique identifier for the AuthorizationService. |
| ServiceCertificate | The complete chain of Certificates used to to validate the AccessTokens provided by the AuthorizationService. |
| UserTokenPolicies | The UserIdentityTokens accepted by the AuthorizationService. |
Method Result Codes (defined in Call Service)
| Result Code | Description |
| Bad_UserAccessDenied | The current user does not have the rights required. |
Table 153 specifies the AddressSpace representation for the GetServiceDescription Method.
| Attribute | Value | ||||
| BrowseName | 2:GetServiceDescription | ||||
| References | NodeClass | BrowseName | DataType | TypeDefinition | ModellingRule |
|---|---|---|---|---|---|
| 0:HasProperty | Variable | 0:OutputArguments | 0:Argument[] | 0:PropertyType | Mandatory |
9.6.10 AccessTokenRequestedAuditEventType
This event is raised when a AccessToken is requested as a result of a FinishRequestToken Method being called.
This Event and its subtypes are security related and Servers shall only report them to users authorized to view security related audit events.
Its representation in the AddressSpace is formally defined in Table 155.
| References | NodeClass | BrowseName | DataType | TypeDefinition | Modelling Rule |
|---|---|---|---|---|---|
| Attribute | Value | ||||
| BrowseName | 2:AccessTokenRequestedAuditEventType | ||||
| IsAbstract | True | ||||
| Subtype of the 0:AuditUpdateMethodEventType defined in OPC 10000-5. | |||||
| Conformance Units | |||||
|---|---|---|---|---|---|
| GDS Authorization Service Server |
This EventType inherits all Properties of the AuditUpdateMethodEventType. Their semantic is defined in OPC 10000-5.
9.6.11 AccessTokenIssuedAuditEventType
This event is raised when a AccessToken is issued.
This is the result of a RequestAccessToken Method completing.
This Event and its subtypes are security related and Servers shall only report them to users authorized to view security related audit events.
Its representation in the AddressSpace is formally defined in Table 155.
| References | NodeClass | BrowseName | DataType | TypeDefinition | Modelling Rule |
|---|---|---|---|---|---|
| Attribute | Value | ||||
| BrowseName | 2:AccessTokenIssuedAuditEventType | ||||
| IsAbstract | True | ||||
| Subtype of the 0:AuditUpdateMethodEventType defined in OPC 10000-5. | |||||
| Conformance Units | |||||
|---|---|---|---|---|---|
| GDS Authorization Service Server |
This EventType inherits all Properties of the AuditUpdateMethodEventType. Their semantic is defined in OPC 10000-5.
9.7 Information Model for Configuring Servers
9.7.1 Overview
The information model used to provide Servers with the information used to accept AccessTokens from AuthorizationServices in Figure 34.
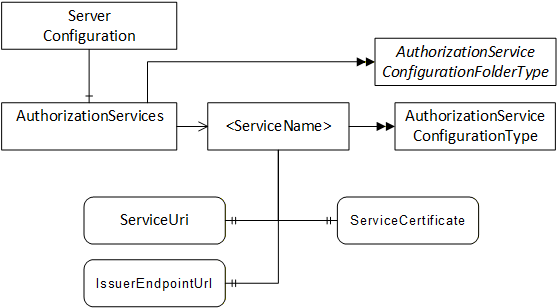
If a Server is also a Client that has to access the AuthorizationService, the necessary KeyCredentials can be provided with the push configuration management model (see 8.4).
9.7.2 AuthorizationServiceConfigurationFolderType
This ObjectType represents a folder that contains AuthorizationServiceConfiguration Objects which may be accessed via the Server. It is defined in Table 156.
| Attribute | Value | |||
| BrowseName | 0:AuthorizationServicesConfigurationFolderType | |||
| IsAbstract | False | |||
| References | NodeClass | BrowseName | TypeDefinition | Modelling Rule |
|---|---|---|---|---|
| Subtype of the 0:FolderType defined in OPC 10000-5. | ||||
| 0:HasComponent | Object | 0:<ServiceName> | 0:AuthorizationService ConfigurationType | OptionalPlaceholder |
| Conformance Units | ||||
|---|---|---|---|---|
| Authorization Service Configuration Server |
9.7.3 AuthorizationServices
This Object is an instance of AuthorizationServicesConfigurationFolderType. It contains The AuthorizationServiceConfiguration Objects which may be accessed via the Server. It is the target of an HasComponent reference from the ServerConfiguration Object defined in 7.10.4. It is defined in Table 157.
| Attribute | Value | |||
| BrowseName | 0:AuthorizationServices | |||
| TypeDefinition | 0:AuthorizationServicesConfigurationFolderType defined in 9.6.2. | |||
| References | NodeClass | BrowseName | TypeDefinition | Modelling Rule |
|---|---|---|---|---|
| Conformance Units | ||||
|---|---|---|---|---|
| Authorization Service Configuration Server |
9.7.4 AuthorizationServiceConfigurationType
This ObjectType is the TypeDefinition for an Object that allows the configuration of an AuthorizationService used by a Server. It is defined in Table 158.
| Attribute | Value | ||||
| BrowseName | 0:AuthorizationServiceConfigurationType | ||||
| IsAbstract | False | ||||
| References | NodeClass | BrowseName | DataType | TypeDefinition | Modelling Rule |
|---|---|---|---|---|---|
| Subtype of the 0:BaseObjectType defined in OPC 10000-5. | |||||
| 0:HasProperty | Variable | 0:ServiceUri | 0:String | 0:PropertyType | Mandatory |
| 0:HasProperty | Variable | 0:ServiceCertificate | 0:ByteString | 0:PropertyType | Mandatory |
| 0:HasProperty | Variable | 0:IssuerEndpointUrl | 0:String | 0:PropertyType | Mandatory |
| Conformance Units | |||||
|---|---|---|---|---|---|
| Authorization Service Configuration Server |
The ServiceUri Property uniquely identifies the AuthorizationService.
The ServiceCertificate Property has the Certificate(s) used to verify AccessTokens issued by the AuthorizationService. The value is the complete chain of Certificate used for verification (see OPC 10000-6 for information on encoding chains).
The IssuerEndpointUrl is the value of the IssuerEndpointUrl in UserTokenPolicies which require the use of the AuthorizationService. The contents of this field depend on the AuthorizationService and are described in OPC 10000-6.
9.7.5 AuthorizationServiceConfigurationDataType
This type is used to serialize the AuthorizationService configuration. It is defined in Table 159.
This type is used as part of the ApplicationConfigurationDataType defined in 7.10.19 which allows multiple of AuthorizationServices in a Server to be updated at once.
The Name of the record is the name portion of the BrowseName of the associated AuthorizationServiceConfiguration Object in the AddressSpace.
If multiple ServiceCertificates are specified the first entry in the list is exposed with the ServerCertificate Property on the AuthorizationServiceConfiguration Object.
Note that when a new AuthorizationServiceConfiguration is added, Clients need to browse the AuthorizationServices folder to discover the NodeId assigned by the Server that is needed for Certificate Management Methods.
| Name | Type | Description |
| AuthorizationServiceConfigurationDataType | Structure | |
| ServiceUri | 0:UriString | A URI uniquely identifies the AuthorizationService. |
| ServiceCertificates | 0:ServiceCertificateDataType[] | A list of Certificates used by the AuthorizationService to verify AccessTokens. |
Certificate | 0:ByteString | The Certificate needed to verify AccessTokens issued by the AuthorizationService. |
Issuers | 0:ByteString[] | The Issuers needed to verify the Certificate. The Certificates appear in the array starting with the issuer of the Certificate. The CRLs are not part of to the AuthorizationService configuration so the administration Client shall check any CRLs and update the configuration if a Certificate in the chain is revoked. |
ValidFrom | 0:UtcTime | When the Certificate may be used to verify AccessTokens. If null then the Certificate can be used any time after ValidFrom field within the Certificate. |
ValidTo | 0:UtcTime | After this time, the Certificate may not be used to verify AccessTokens. If null there is no expiry time other than the ValidTo field within the Certificate. |
| IssuerEndpointSettings | 0:String | The AuthorizationService specific settings that Clients need to know before requesting AccessTokens from the AuthorizationService. The syntax depends on the AuthorizationService. |
Its representation in the AddressSpace is defined in Table 160.
| Attribute | Value | |||||
| BrowseName | 0:AuthorizationServiceConfigurationDataType | |||||
| IsAbstract | False | |||||
| References | NodeClass | BrowseName | DataType | TypeDefinition | Other | |
|---|---|---|---|---|---|---|
| Subtype of the 0:BaseConfigurationRecordDataType defined in 7.8.5.5. | ||||||
| Conformance Units | ||||||
|---|---|---|---|---|---|---|
| Authorization Service Configuration Server |
