This is a work group under VDMA Integrated Assembly Solutions department. The purpose of the IJT group is to define data models and data access standards for various joining techniques such as Tightening, Gluing, Riveting, Flow Drill Fastening, etc.
Assembling products by joining parts together is a key operation in many industries. There are obviously countless differences between gluing, welding, riveting, etc., but also surprisingly many characteristics that all share.
- There is often a tool that executes the joining.
- There is often some device controlling the joining process such as a processor, computer, or PLC.
- There is often a program of some sort that govern the joining process.
- There is often a digital result of the joining process that may both influence the overlying assembly process and be stored to provide product traceability.
- There could be an operator guidance to help the operator determine the steps involved in the joining process.
- There could be a representation of the joint as part of the digital twin of the product being assembled.
- There is often a need from external systems to select or influence the joining operation, such an MES system, a station PLC, location system, or a barcode scanner.
The Industrial Joining Technology companion specification endeavors to find the best balance between the models used in all joining technologies and the models specific to an area.
Joining is often tightly connected with other industrial processes such as vision (for identification), or robotics (for location), so special attention has been put on harmonization with other VDMA companion specifications, in order to strive for seamless integration from a customer’s perspective.
Every joining technique will define their own standard specification with some of the common types which will be re-used across the joining techniques.
Example: Result is minimal data content which is intended to be common for other techniques as well.
The following figure describes the taxonomy of the Industrial Joining Technologies workgroup.
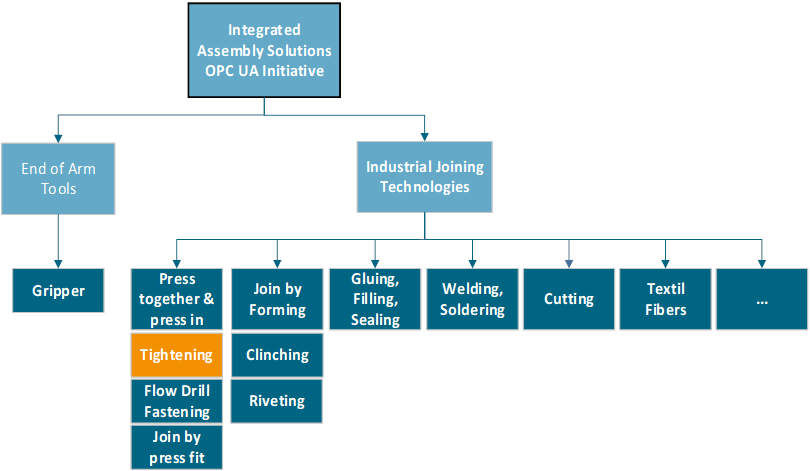
Figure 1 - Overview of IJT Initiative
Joining System
The idea of joining system is to represent different types of systems for each joining technique using a common interface.
A joining system could include Tightening, Gluing, Riveting and more systems.
Tightening System
The idea of a tightening system is to represent an easy to understand entity that can manage tightening processes autonomously, forming single point of contact for external systems.
Usually a tightening process drives threaded fastener in a counterpart. This is most likely done by the rotation of one of the fastener parts. By doing so, there is a tension force applied to the materials, which are meant to get fastened. Hereby the process will be controlled and supervised by the controller. There are numerous parameters and boundaries which may be set and measurements which are taken during the tightening process.
The measurement data and results are of eminent importance for the assessment of the process quality. This data should mostly be made available to higher-level systems.
In addition to the core process of tightening, other supporting functionalities exist in a tightening system. These are, for example, the advance of the bit, socket, or the supply of the fastening elements.
The tightening system should be able to represent the many different forms of systems that exists today and allow freedom to be extended as more become available.
The core asset in a tightening system is a controller which handles also the OPC UA communication. The definition of the controller is kept wide by design. It could be a server, a PLC, an embedded processor, etc.
Some of the tightening systems that exists today are:
- A physical controller, managing a cable handheld tool and a set of battery handheld tools.
- A physical controller managing several battery tools
- A battery tool containing a controller
- A controller managing several fixtured spindles
- A controller managing a spindle, a screw feeder and a screw feeder controller mounted on a robot (The robot is not part of the tightening system)
- A clutch tool reporting OK/NOT_OK.
- A computer system storing and providing historical results or visualizing the information.
OPC UA is an open and royalty free set of standards designed as a universal communication protocol. While there are numerous communication solutions available, OPC UA has key advantages:
- A state of art security model (see OPC 10000-2).
- A fault tolerant communication protocol.
- An information modelling framework that allows application developers to represent their data in a way that makes sense to them.
OPC UA has a broad scope which delivers for economies of scale for application developers. This means that a larger number of high-quality applications at a reasonable cost are available. When combined with semantic models such as OPC UA for Tightening System, OPC UA makes it easier for end users to access data via generic commercial applications.
The OPC UA model is scalable from small devices to ERP systems. OPC UA Servers process information locally and then provide that data in a consistent format to any application requesting data - ERP, MES, PMS, Maintenance Systems, HMI, Smartphone or a standard Browser, for examples. For a more complete overview see OPC 10000-1.
As an open standard, OPC UA is based on standard internet technologies, like TCP/IP, HTTP, Web Sockets.
As an extensible standard, OPC UA provides a set of Services (see OPC 10000-4) and a basic information model framework. This framework provides an easy manner for creating and exposing vendor defined information in a standard way. More importantly all OPC UA Clients are expected to be able to discover and use vendor-defined information. This means OPC UA users can benefit from the economies of scale that come with generic visualization and historian applications. This specification is an example of an OPC UA Information Model designed to meet the needs of developers and users.
OPC UA Clients can be any consumer of data from another device on the network to browser based thin clients and ERP systems. The full scope of OPC UA applications is shown in Figure 2.
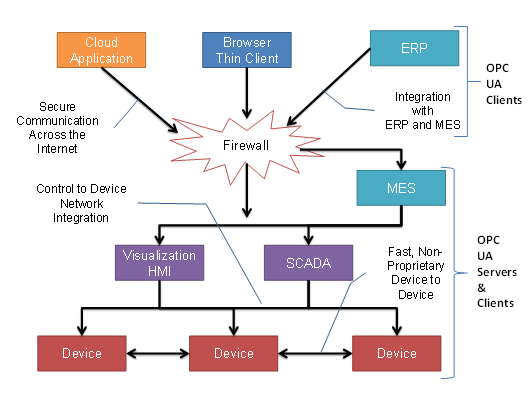
Figure 2 - The Scope of OPC UA within an Enterprise
OPC UA provides a robust and reliable communication infrastructure having mechanisms for handling lost messages, failover, heartbeat, etc. With its binary encoded data, it offers a high-performing data exchange solution. Security is built into OPC UA as security requirements become more and more important especially since environments are connected to the office network or the internet and attackers are starting to focus on automation systems.
OPC UA provides a framework that can be used to represent complex information as Objects in an AddressSpace which can be accessed with standard services. These Objects consist of Nodes connected by References. Different classes of Nodes convey different semantics. For example, a Variable Node represents a value that can be read or written. The Variable Node has an associated DataType that can define the actual value, such as a string, float, structure etc. It can also describe the Variable value as a variant. A Method Node represents a function that can be called. Every Node has a number of Attributes including a unique identifier called a NodeId and non-localized name called as BrowseName. An Object representing a ‘Reservation’ is shown in Figure 3.
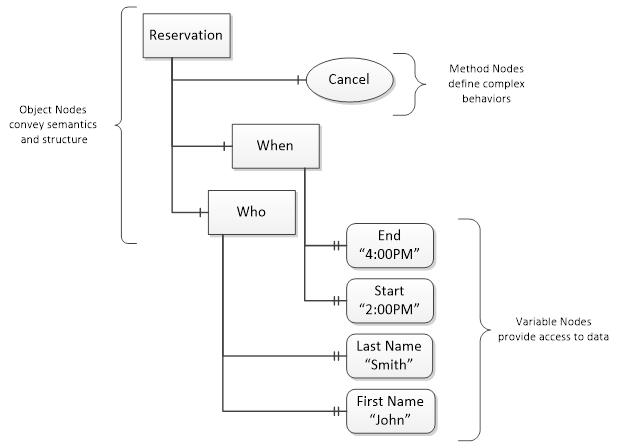
Figure 3 - A Basic Object in an OPC UA Address Space
Object and Variable Nodes represent instances and they always reference a TypeDefinition (ObjectType or VariableType) Node which describes their semantics and structure. Figure 4 illustrates the relationship between an instance and its TypeDefinition.
The type Nodes are templates that define all of the children that can be present in an instance of the type. In the example in Figure 4 the PersonType ObjectType defines two children: First Name and Last Name. All instances of PersonType are expected to have the same children with the same BrowseNames. Within a type the BrowseNames uniquely identify the children. This means Client applications can be designed to search for children based on the BrowseNames from the type instead of NodeIds. This eliminates the need for manual reconfiguration of systems if a Client uses types that multiple Servers implement.
OPC UA also supports the concept of sub-typing. This allows a modeller to take an existing type and extend it. There are rules regarding sub-typing defined in OPC 10000-3, but in general they allow the extension of a given type or the restriction of a DataType. For example, the modeller may decide that the existing ObjectType in some cases needs an additional Variable. The modeller can create a subtype of the ObjectType and add the Variable. A Client that is expecting the parent type can treat the new type as if it was of the parent type. Regarding DataTypes, subtypes can only restrict. If a Variable is defined to have a numeric value, a sub type could restrict it to a float.
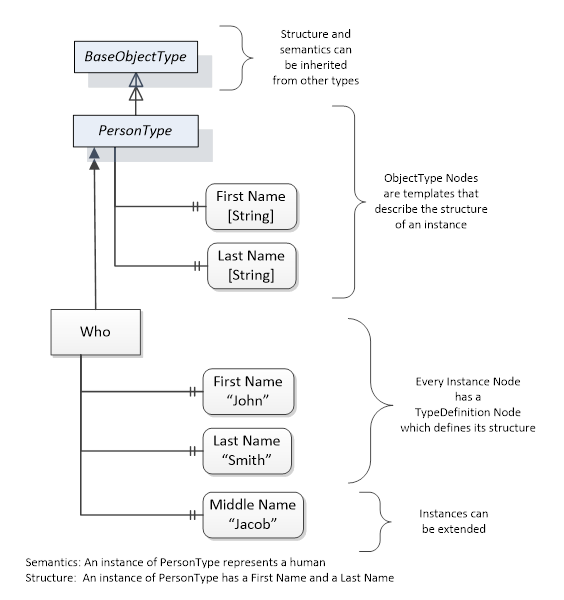
Figure 4 - The Relationship between Type Definitions and Instances
References allow Nodes to be connected in ways that describe their relationships. All References have a ReferenceType that specifies the semantics of the relationship. References can be hierarchical or non-hierarchical. Hierarchical references are used to create the structure of Objects and Variables. Non-hierarchical are used to create arbitrary associations. Applications can define their own ReferenceType by creating subtypes of an existing ReferenceType. Subtypes inherit the semantics of the parent but may add additional restrictions. Figure 5 depicts several References, connecting different Objects.
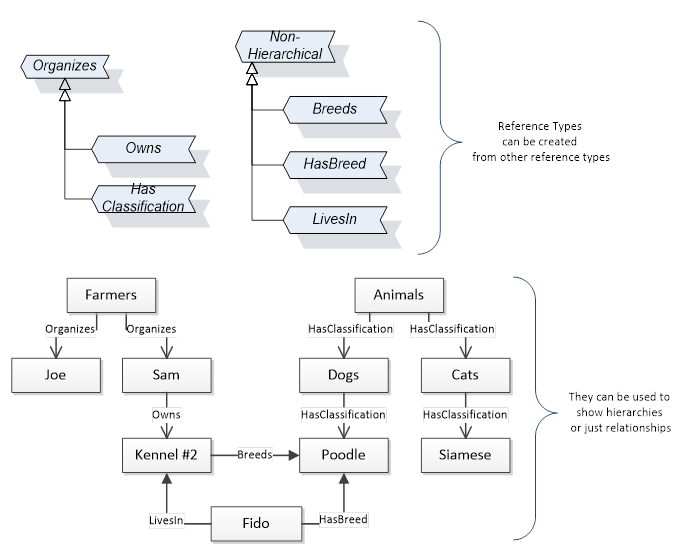
Figure 5 - Examples of References between Objects
The figures above use a notation that was developed for the OPC UA specification. The notation is summarized in Figure 6. UML representations can also be used; however, the OPC UA notation is less ambiguous because there is a direct mapping from the elements in the figures to Nodes in the AddressSpace of an OPC UA Server.
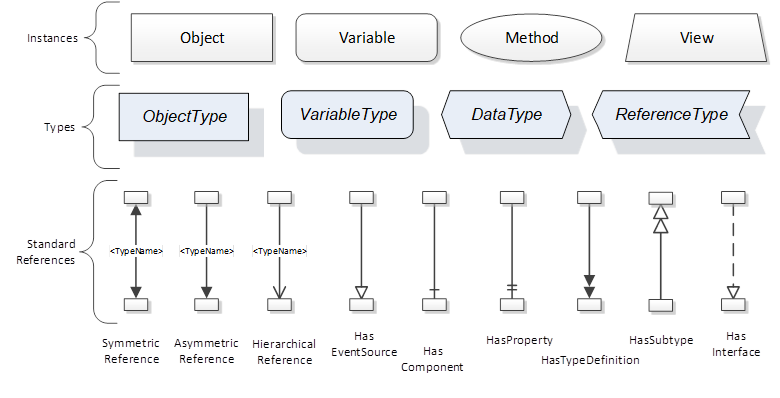
Figure 6 - The OPC UA Information Model Notation
A complete description of the different types of Nodes and References can be found in OPC 10000-3 and the base structure is described in OPC 10000-5.
OPC UA specification defines a very wide range of functionality in its basic information model. It is not required that all Clients or Servers support all functionality in the OPC UA specifications. OPC UA includes the concept of Profiles, which segment the functionality into testable certifiable units. This allows the definition of functional subsets (that are expected to be implemented) within a companion specification. The Profiles do not restrict functionality, but generate requirements for a minimum set of functionality (see OPC 10000-7).
OPC UA allows information from many different sources to be combined into a single coherent AddressSpace. Namespaces are used to make this possible by eliminating naming and id conflicts between information from different sources. Each namespace in OPC UA has a globally unique string called a NamespaceUri which identifies a naming authority and a locally unique integer called a NamespaceIndex, which is an index into the Server's table of NamespaceUris. The NamespaceIndex is unique only within the context of a Session between an OPC UA Client and an OPC UA Server- the NamespaceIndex can change between Sessions and still identify the same item even though the NamespaceUri's location in the table has changed. The Services defined for OPC UA use the NamespaceIndex to specify the Namespace for qualified values.
There are two types of structured values in OPC UA that are qualified with NamespaceIndexes: NodeIds and QualifiedNames. NodeIds are locally unique (and sometimes globally unique) identifiers for Nodes. The same globally unique NodeId can be used as the identifier in a node in many Servers – the node's instance data may vary but its semantic meaning is the same regardless of the Server it appears in. This means Clients can have built-in knowledge of what the data means in these Nodes. OPC UA Information Models generally define globally unique NodeIds for the TypeDefinitions defined by the Information Model.
QualifiedNames are non-localized names qualified with a Namespace. They are used for the BrowseNames of Nodes and allow the same names to be used by different information models without conflict. TypeDefinitions are not allowed to have children with duplicate BrowseNames; however, instances do not have that restriction.
An OPC UA companion specification for an industry specific vertical market describes an Information Model by defining ObjectTypes, VariableTypes, DataTypes and ReferenceTypes that represent the concepts used in the vertical market, and potentially also well-defined Objects as entry points into the AddressSpace.