The implicit authorization use case describes how the Client’s ApplicationInstance Certificate and any UserIdentityToken associated with the Session is used to determine whether an AccessToken is permitted and what claims are available. This use case is illustrated in Figure 30.
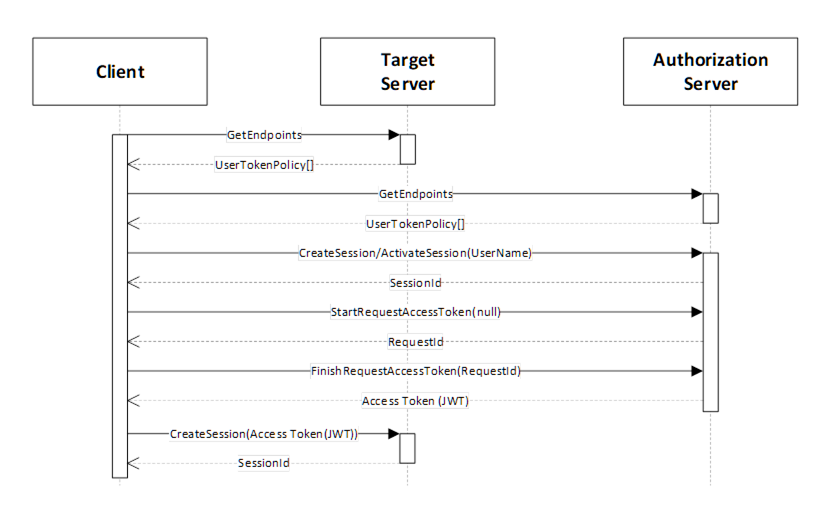
Figure 30 – Implicit Authorization
The "Target Server" is the Server that the Client wishes to access. It publishes a UserTokenPolicy that indicates that it accepts AccessTokens from an "Authorization Server". The parameters needed to connect to the "Authorization Server" are stored in the IssuerEndpointUrl field of the UserTokenPolicy and are defined in OPC 10000-6. These parameters are specified as a JSON object rather than a URL as implied by the field name and requirements specific to AuthorizationServices are defined in Table 144.
Table 144 – Target Server UserTokenPolicy Parameters
|
Name |
Description |
|
IssuerEndpointUrl ua:authorityUrl |
The URL of the "Authorization Server". |
|
IssuerEndpointUrl ua:tokenEndpoint |
The NodeId of the AuthorizationService Object encoded using the URI qualified syntax defined in OPC 10000-6. |
|
IssuerEndpointUrl ua:authorizationEndpoint |
The NodeId of the UserTokenPolicies Property. Shall be null if Implicit Authorization is required. Shall be non-null if Explicit Authorization is required (see 9.4). |
The Client shall be trusted by the "Authorization Server" and could require the Client to present user credentials. These credentials can be provided to the Client out-of-band (e.g. an administrator specified them in the Client configuration file). The user credentials used can be any type of user credential including X.509 and JWT.
The Session with the "Authorization Server" may be created explicitly with a call to CreateSession or it can be implicit via a Session-less Method Call.
With this use case, the Client uses the EndpointDescriptions provided by the "Authorization Server" to determine what credentials to provide when creating a Session.
The Client then calls the StartRequestToken and FinishRequestToken Methods on the AuthorizationService Object. The "Authorization Server" determines if the Client is permitted to receive an AccessToken and populates it with any claims granted to the Client.
The AccessToken includes a list of network Roles granted to the Client. The network Roles are abstract Roles defined by the system administrator that are mapped onto the Roles supported by each Target Server with IdentityMappingRules set by the administrator (see OPC 10000-18).
Once the Client has the AccessToken, it passes the AccessToken to the Target Server which validates the AccessToken, as described in OPC 10000-4. The Target Server is configured out-of-band with the Certificate used to validate the AccessTokens issued by the Authorization Server.