The original RSA based profiles used AsymmetricEncryption to negotiate the symmetric keys used for the SecureChannel. Diffie-Hellman Key Agreement (RSA-DH) allows for key negotiation using the same pattern as defined for ECC in Clause 6.8. This approach provides perfect forward secrecy for RSA based profiles and is generally preferred for modern systems.
The OpenSecureChannel Request and Response messages are signed but not encrypted when using RSA-DH.
When creating an EncryptedSecret, the DH PublicKeys are exchanged using the mechanisms defined for ECC in 6.8.2. This includes using the misnamed EccEncryptedSecret and the AdditionalHeader key names defined in Table 70.
The RSA-DH Key Negotiation process is show in Figure 17.
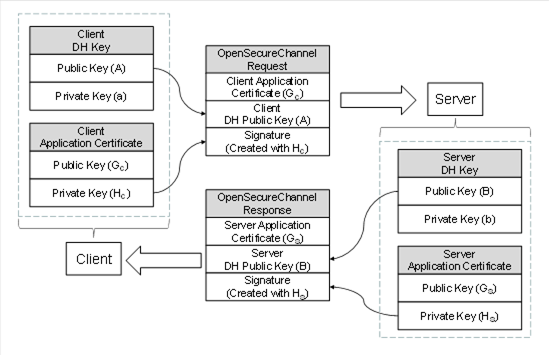
Figure 17 – RSA-DH Key Negotiation
To negotiate the keys used for the SecureChannel a finite field group is determined by the PublicKey lengths allowed by the SecurityPolicy. The finite field groups are defined in IETF RFC 7919. The mapping to finite field groups is shown in Table 72.
Table 72 – Finite Field Group Selection
|
RSA PublicKey Length (bits) |
Finite Group |
Nonce Length (bytes) |
DH PrivateKey (bits) |
|
2048-4096 |
ffdhe3072 |
384 |
275 |
The RSA PublicKey Length is the minimum key length for Certificate PublicKeys allowed by the SecurityPolicy.
The choice of group determines the DH parameters to use (p and g which are constants defined in IETF RFC 7919). The DH PrivateKey length from Table 72 is used to generate a random number (a) of that length.
The Client then calculates the DH PublicKey (a.k.a. Nonce) with:
A = ga mod p
The ClientNonce (A) is encoded as zero padded big-endian OctetString.
Similarly, the Server the generates a random number (b). It then calculates the DH PublicKey with:
B = gb mod p
The ServerNonce (B) is encoded as zero padded big-endian OctetString.
The shared secret is calculated by the Client with:
IKM = Ba mod p
The shared secret is calculated by the Server with:
IKM = Ab mod p
Once the shared secret (IKM) is computed the rest of the key derivation process is identical to the ECC starting with Step 2 described in 6.8.1.