Clause 8 specifies the OPC UA Information Model for a Security Key Service (SKS). The functionality and behaviour of an SKS is described in 5.4.4. It defines the distribution framework for cryptographic keys used for message security. A Publisher or Subscriber can pull the keys from the SKS or the SKS can push the keys to the Publisher or Suscriber. The sequences for pull and push are described in 5.4.4.3.
The SKS can be a network service used to manage keys for all Publishers and Subscribers or it can be part of a Publisher to manage the keys for the NetworkMessages sent by this Publisher.
Figure 36 depicts the ObjectTypes and their components used to represent the SKS functionality in the PublishSubscribe Object.
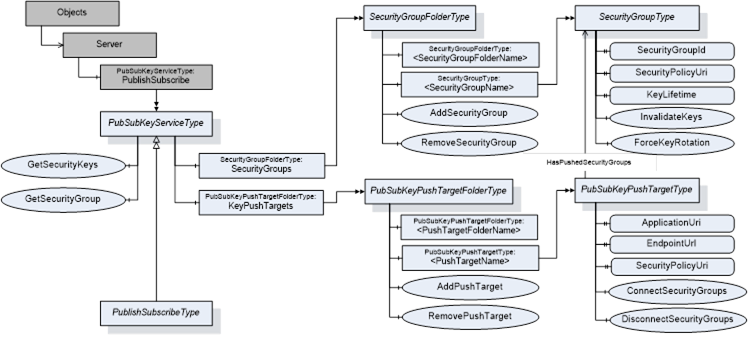
Figure 36 – PublishSubscribe Object Types overview
The PublishSubscribe Object is the root node for all PubSub related configuration Objects. It is an instance of the PubSubKeyServiceType or the PublishSubscribeType and a component of the Server Object.
The PubSubKeyServiceType defines the Method for pull access to security keys and the related management of SecurityGroups. This ObjectType is used for the PublishSubscribe Object if only the Security Key Service functionality is provided. If the PubSub configuration functionality is provided, the PublishSubscribeType is used instead.
A SecurityGroup manages keys used for securing PubSub NetworkMessages. The SecurityGroups are organized by the SecurityGroupFolderType and represented by instances of the SecurityGroupType.
A PubSubKeyPushTarget is a Server to which the SKS should push keys. Each push target is related to a list of SecurityGroups.
The push targets are organized by the PubSubKeyPushTargetFolderType and represented by instances of the PubSubKeyPushTargetType. These instances are used by the SKS to push the security keys for related SecurityGroups into the Publisher or Subscriber.
The PublishSubscribeType contains the entry points for the PubSub configuration model defined in clause 9.