Errata exists for this version of the document.
The term message is used with various intentions in the messaging world. It sometimes only refers to the payload (the application data) and sometimes to the network packet that also includes protocol-, security-, or encoding-specific data. To avoid confusion, this specification formally defines the term DataSetMessage to mean the application data (the payload) supplied by the Publisher and the term NetworkMessage to mean the message handed off and received from a specific Message Oriented Middleware. DataSetMessages are embedded in NetworkMessages. Figure 4 shows the relationship of these message types.
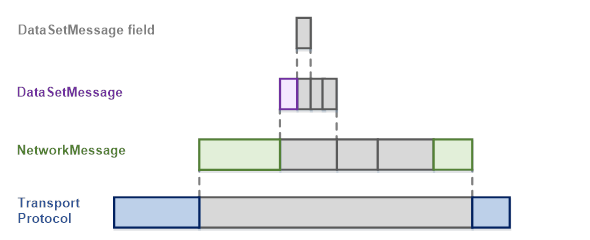
Figure 4 – OPC UA PubSub Message Layers
The transport protocol-specific headers and definitions are described in 7.3.
Following is an abstract definition of DataSetMessage and NetworkMessage. The concrete structure depends on the message mapping and is described in 7.2.
A DataSetMessage field is the representation of a DataSet field in a DataSetMessage.
A DataSet field contains the actual value as well as additional information about the value like status and timestamp.
A DataSet field can be represented as a DataValue, as a Variant or as a RawData in the DataSetMessage field. The representation depends on the DataSetFieldContentMask defined in 6.2.3.2.
The representation as a DataValue is used if value, status and timestamp should be included in the DataSetMessage.
The representation as Variant is used if value or bad status should be included in the DataSetMessage.
The representation as RawData is the most efficient format and is used if a common status and timestamp per DataSet is sufficient.
A DataSetMessage is created from a DataSet. It consists of a header and the encoded fields of the DataSet.
Depending on the configured DataSetMessageContentMask, a DataSetMessage may exist in different forms and with varying detail. DataSetMessages do not contain any information about the data acquisition or information source in the Publisher.
Additional header information includes:
DataSetWriterId Identifies the DataSetWriter and indirectly the PublishedDataSet.
Sequence number A number that is incremented for each DataSetMessage. Can be used to verify the ordering and to detect missing messages.
Timestamp A timestamp describing when the data in this DataSetMessage was obtained.
Version Version information about the configuration of the DataSetMetaData.
Status Status information about the data in this DataSetMessage.
Keep alive When no DataSetMessages are sent for a configured time period, a keep alive DataSetMessage is sent to signal the Subscribers that the Publisher is still alive.
Some encodings differentiate between key frame DataSetMessages and delta frame DataSetMessages. A key frame DataSetMessage includes values for all fields of the DataSet. A delta frame DataSetMessage only contains the subset that changed since the previous DataSetMessage.
A key frame DataSetMessage is sent after a configured number of DataSetMessages.
The NetworkMessage is a container for DataSetMessages and includes information shared between DataSetMessages. This information consists of:
PublisherId Identifies the Publisher.
Security data Only available for encodings that support message security. The relevant information is specified in the message mapping.
Promoted fields Selected fields out of the DataSet also sent in the header.
Payload One or more DataSetMessages.
The payload, consisting of the DataSetMessages will be encrypted in accordance with the configured message security. Individual fields of a DataSetMessage can be marked as being “promoted fields”. Such fields are intended for filtering or routing and therefore are never encrypted. How and where the values for promoted fields are inserted depends on the NetworkMessage format and the used protocol. The NetworkMessage header is not encrypted to enable efficient filtering.
Message security in PubSub concerns integrity and confidentiality of the published message payload. The level of security can be:
- No security
- Signing but no encryption
- Signing and encryption
Message security is end-to-end security (from Publisher to Subscriber) and requires common knowledge of the cryptographic keys necessary to sign and encrypt on the Publisher side as well as validate signature and decrypt on the Subscriber side.
The keys used for message security are managed in the context of a SecurityGroup. The basic concepts of a SecurityGroup are described in 5.3.7.
This standard defines a general distribution framework for cryptographic keys. This framework is introduced in 5.4.3.
All parameters that are relevant for message security are described in 6.2.4. These parameters are independent of any Broker level transport security.
The message security for PubSub is independent of the transport protocol mapping and is completely defined by OPC UA.
The transport security is specific to the transport protocol mapping.
When using a broker-based middleware (see 5.4.4.2.2), confidentiality and integrity can be ensured with the transport security between Publishers and the Broker as well as Subscribers and the Broker. The Broker level security in addition requires all Publishers and Subscribers to have credentials that grant them access to a Broker resource.
Transport security may be hop-by-hop security with some risk of man-in-the-middle attacks. It also requires trusting the Broker since the Broker can read the messages. Combining transport security with message security reduces this risk.
A SecurityGroup is an abstraction that represents the message security settings and security keys for a subset of NetworkMessages exchanged between Publishers and Subscribers. The security keys are used to encrypt and decrypt NetworkMessages and to generate and check signatures on a NetworkMessage.
A Security Key Service (SKS) manages SecurityGroups and maintains a mapping between Roles and their access Permissions for a SecurityGroup. This mapping defines if a Publisher or Subscriber has access to the security keys of a SecurityGroup. The SKS is described in more detail in 5.4.3.
A SecurityGroup is identified with a unique identifier called the SecurityGroupId. It is unique within the SKS. A Publisher for its PublishedDataSets must know the SecurityGroupId. For Subscribers the SecurityGroupId is distributed as metadata together with the DataSetMetaData. The metadata for a SecurityGroupId includes the EndpointDescription of the responsible SKS. Publishers and Subscribers use the EndpointDescription to access the SKS and the SecurityGroupId to obtain the security keys for a SecurityGroup.