Push management is performed by using a KeyCredentialConfiguration Object (see 8.5.1) which is a component of the KeyCredentialManagement Folder which is component of the ServerConfiguration Object in a Server. The interactions between the Administration application and the KeyCredentialService during push management are illustrated in Figure 17.
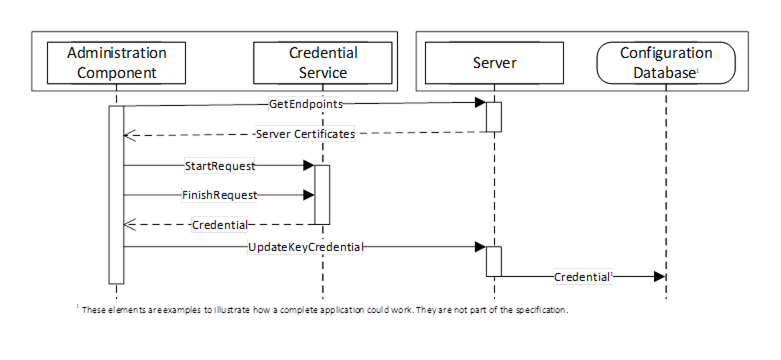
Figure 17 – The Push Model for KeyCredential Management
The Administration Component may use internal APIs to manage KeyCredentials or it could be a standalone utility that uses OPC UA to communicate with a Server which supports the pull model (see 8.2). The Configuration Database is used by the Server to persist its configuration information. The administration and database components are examples to illustrate how an application could be built and are not a requirement.
To ensure security of the KeyCredentials, the KeyCredentialService component can require that secrets be encrypted with a key only known to the intended recipient of the KeyCredentials. For this reason, the Administration Component uses the GetEndpoints Service to read the Certificate from the Server before initiating the credential request on behalf of the Server.
Security, when using the push management model, requires an encrypted channel and the use of administrator credentials for the Server that ensure only authorized users can update KeyCredentials. If the KeyCredentialService component is separate from the Administration Component then different administrator credentials are required for the Server that exposes the that ensure only authorized users can request new KeyCredentials on behalf of Servers.